Reduce triage time by up to 50%
Learn how Guided Triage simplifies network complexities with single-screen triage and AI in our latest blog.

Corelight Announces Cloud Enrichment for AWS, GCP, and Azure

DISRUPT FUTURE ATTACKS WITH
NETWORK EVIDENCE
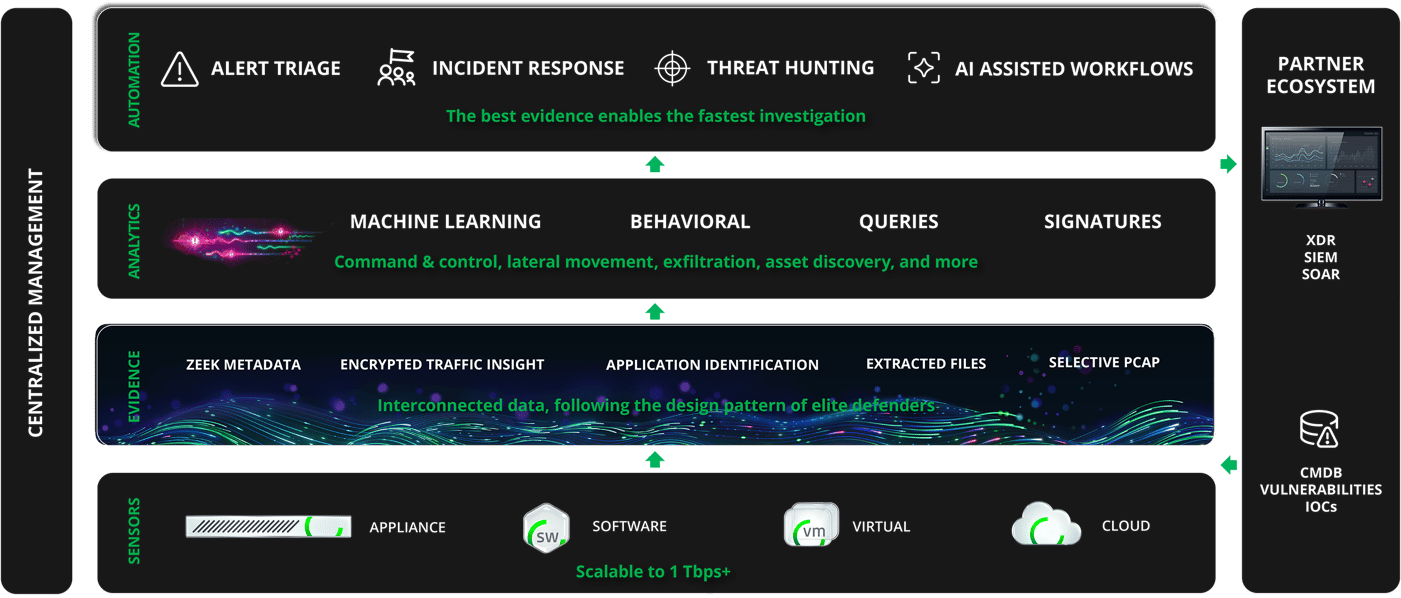
ACCELERATE YOUR DEFENSE. OPEN NETWORK DETECTION AND RESPONSE.
Close the case on ransomware
In high stakes ransomware investigations, many security teams are unable to answer key questions and default to worst-case assumptions. With complete visibility from Corelight, teams can avoid costly overreactions. One customer, when confronted with a $10 million ransomware demand, used Corelight to prove the exfiltrated data being held for ransom had no real value while providing legal aircover for refusing to pay the ransom.
THE BEST EVIDENCE TO FUEL AI-POWERED AUTOMATION