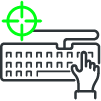
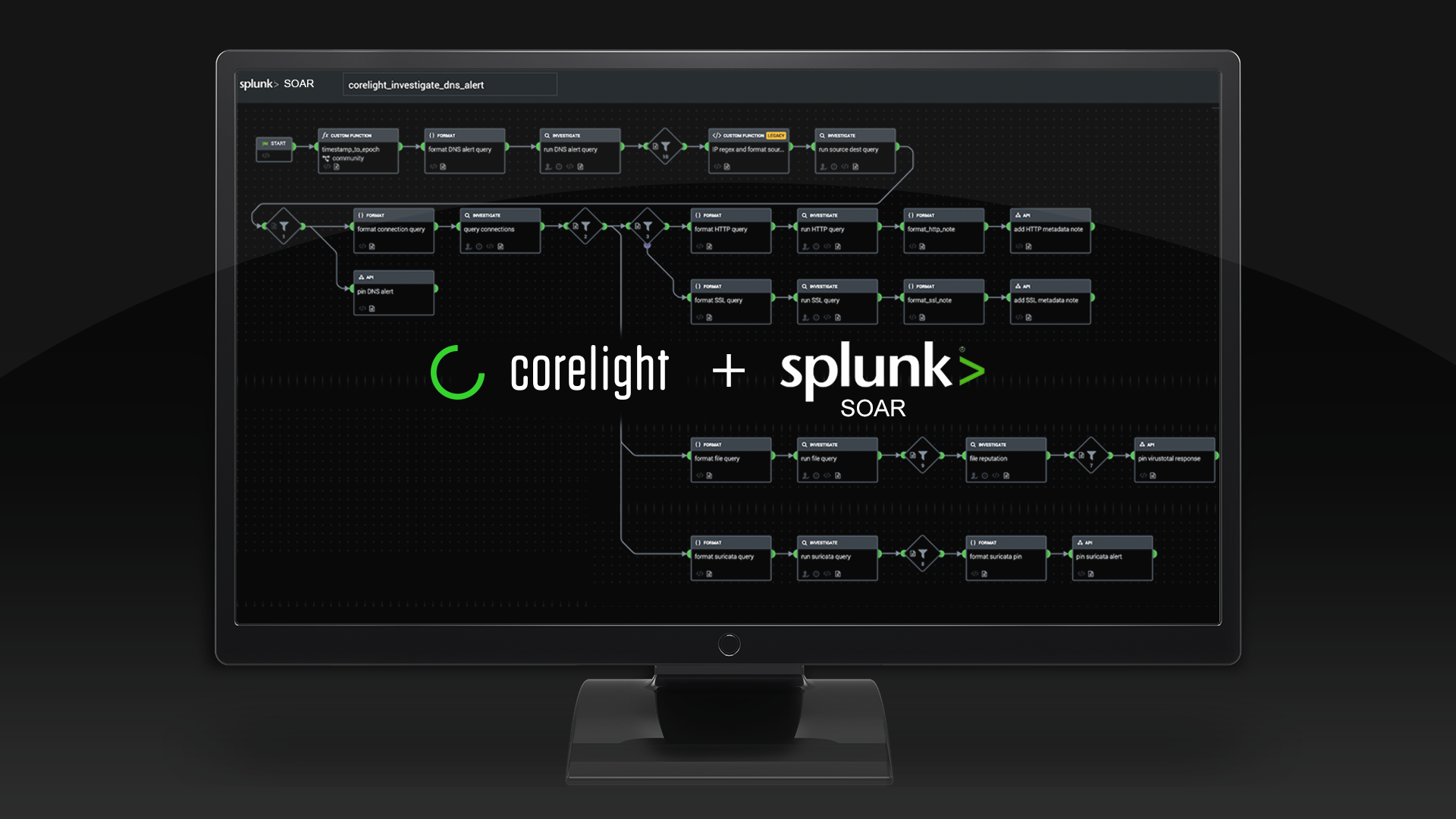
Splunk SOAR + Corelight
Automate your SOC with custom playbooks
Automation gives defenders a scalable, iterative way to build and sustain strategic advantage. With SOAR playbooks powered by Corelight network data, you can finally manage your workload, empower your team, and focus on high-priority work.
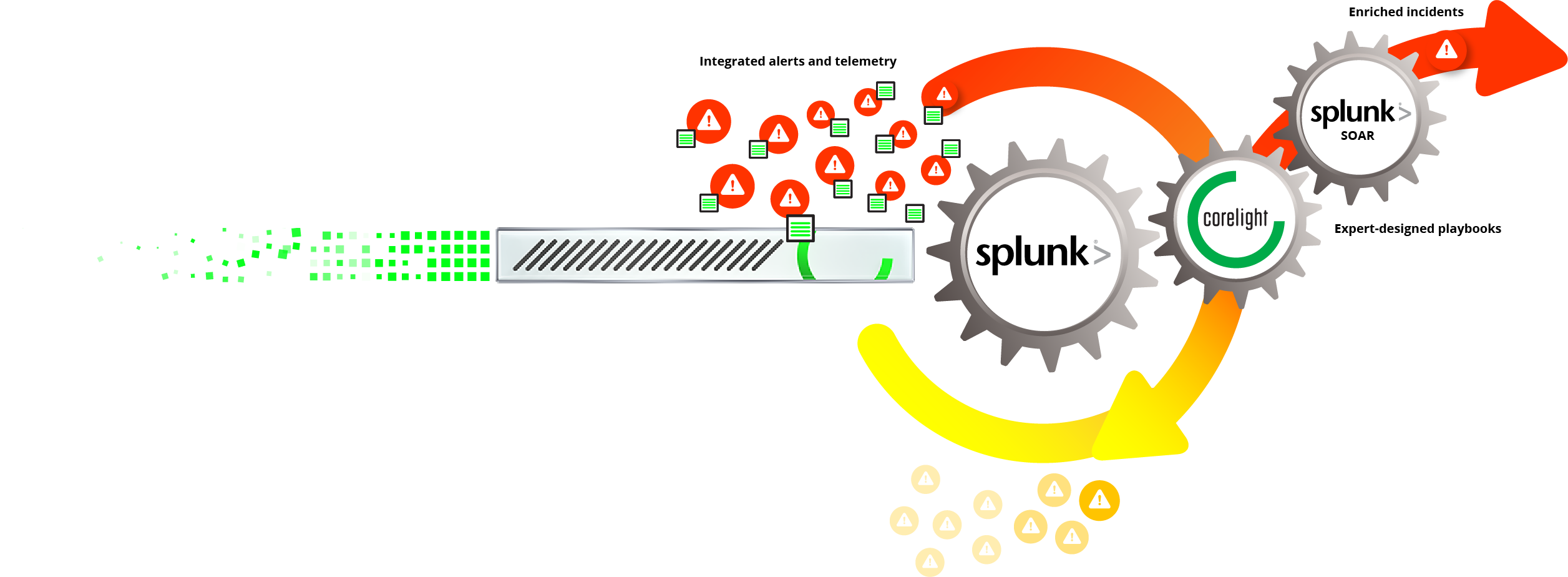
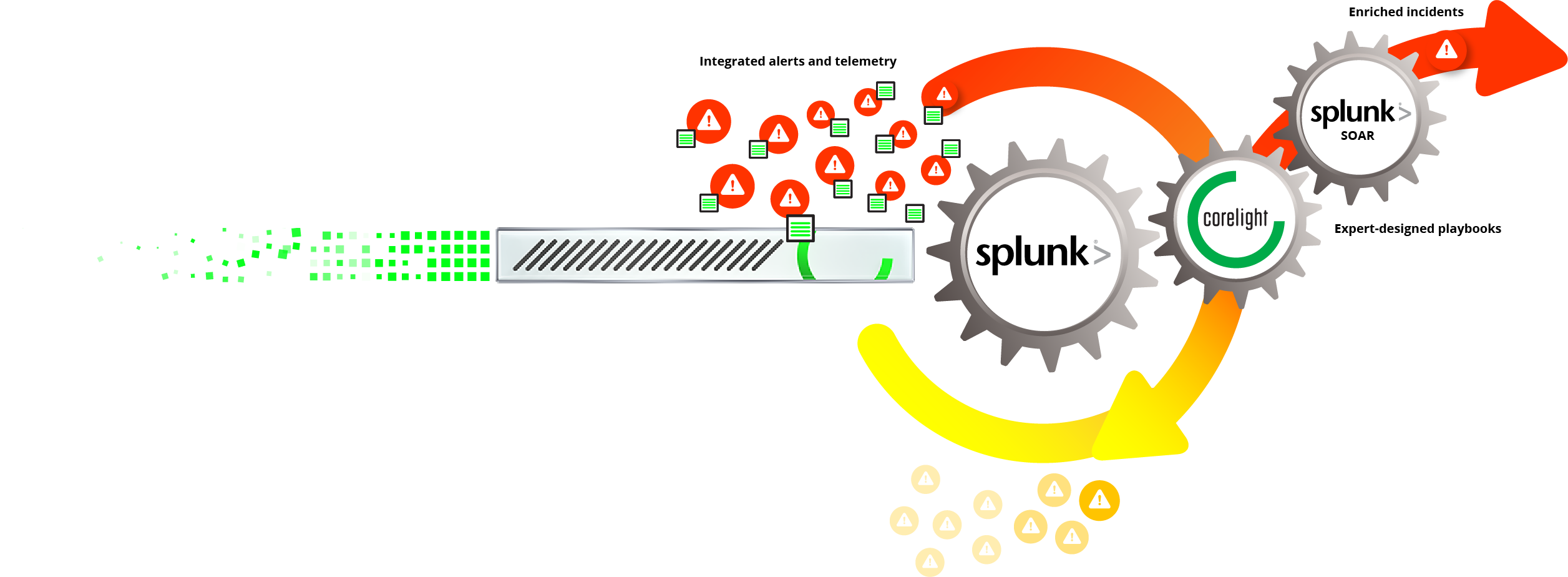
Eliminate 50%+ of alerts before humans see them
Automate data-gathering and alert disposal to save precious time
Help every analyst become equally excellent
Improve decision quality across an inconsistent analyst skill set
Get your analysts ready for bigger challenges
Grow needed critical skill sets faster on the job

Make decisions with excellent vision + guidance
The combination of structured data and expert-designed playbooks from Corelight gives security teams streamlined capabilities to manage security incidents.
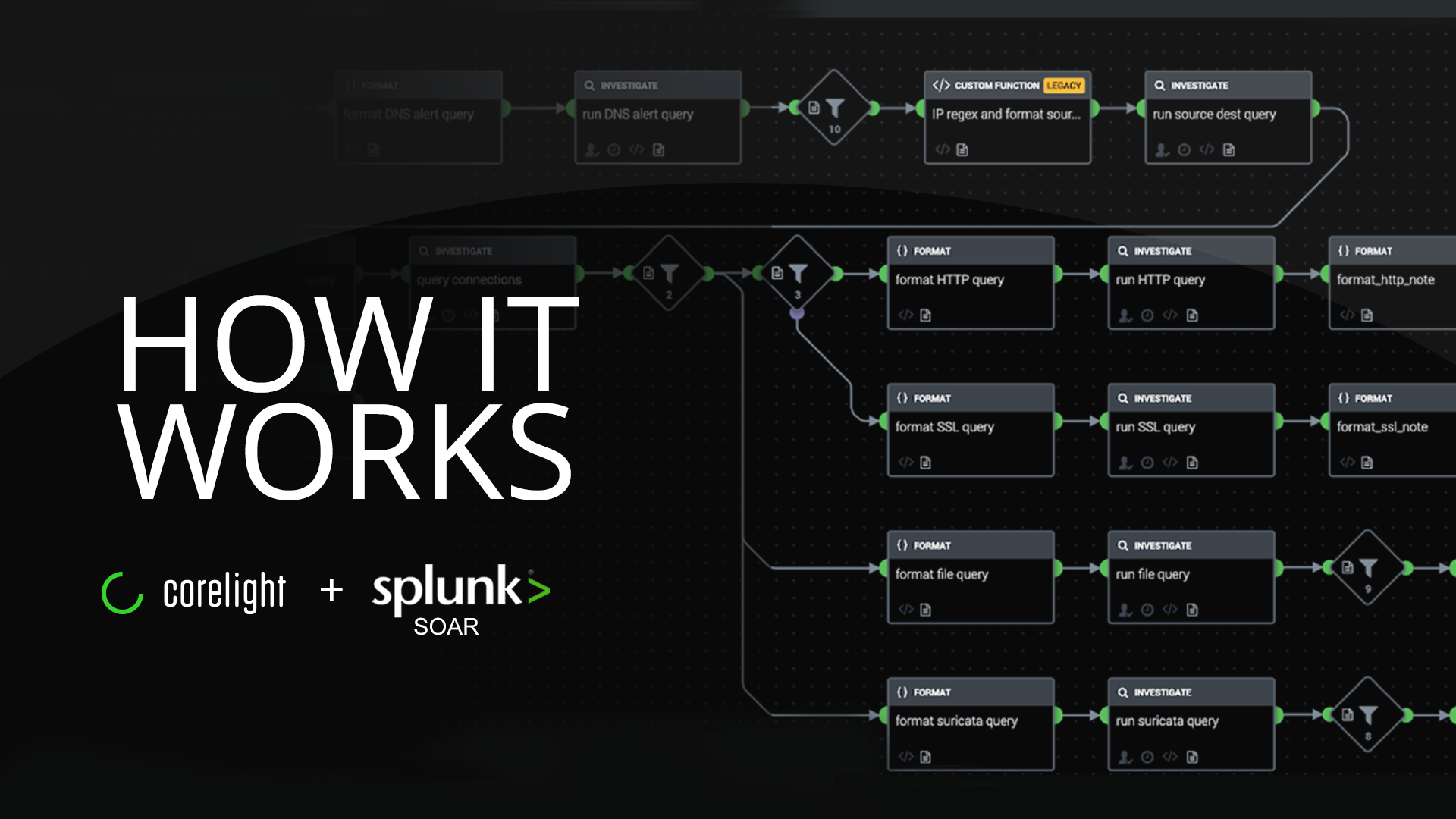
Investigate faster with alerts integrated into evidence
Every Suricata alert contains its associated precorrelated Zeek data to bring foundational, standardized evidence all in one place, speeding investigations.
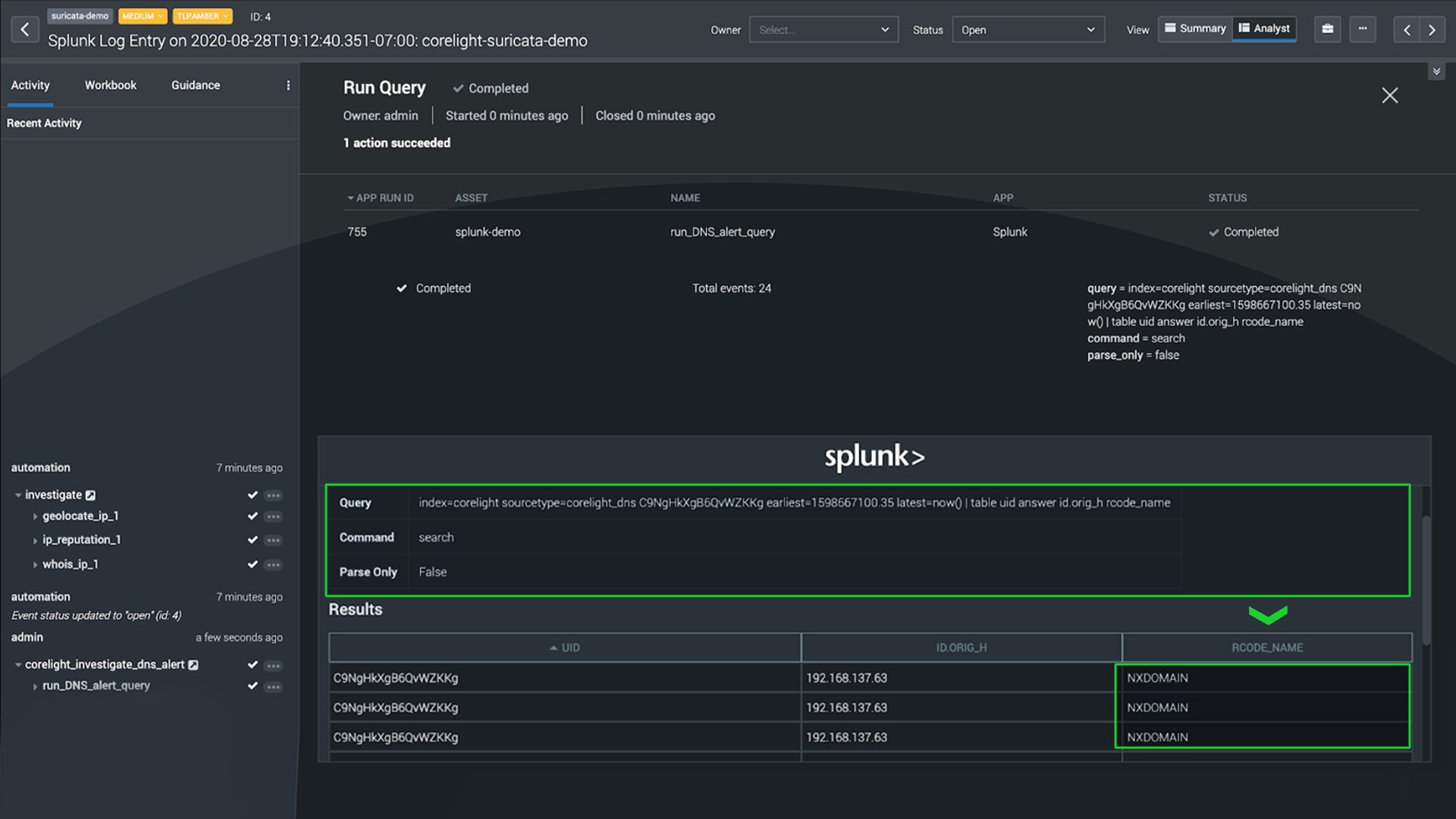
Weed out irrelevant alerts
Often attackers try to compromise systems, but fail to do so. Above, a client tried to connect to a malicious site but it was offline. SOAR plus Corelight data helps analysts see when attacks go nowhere and focus on incidents that matter.
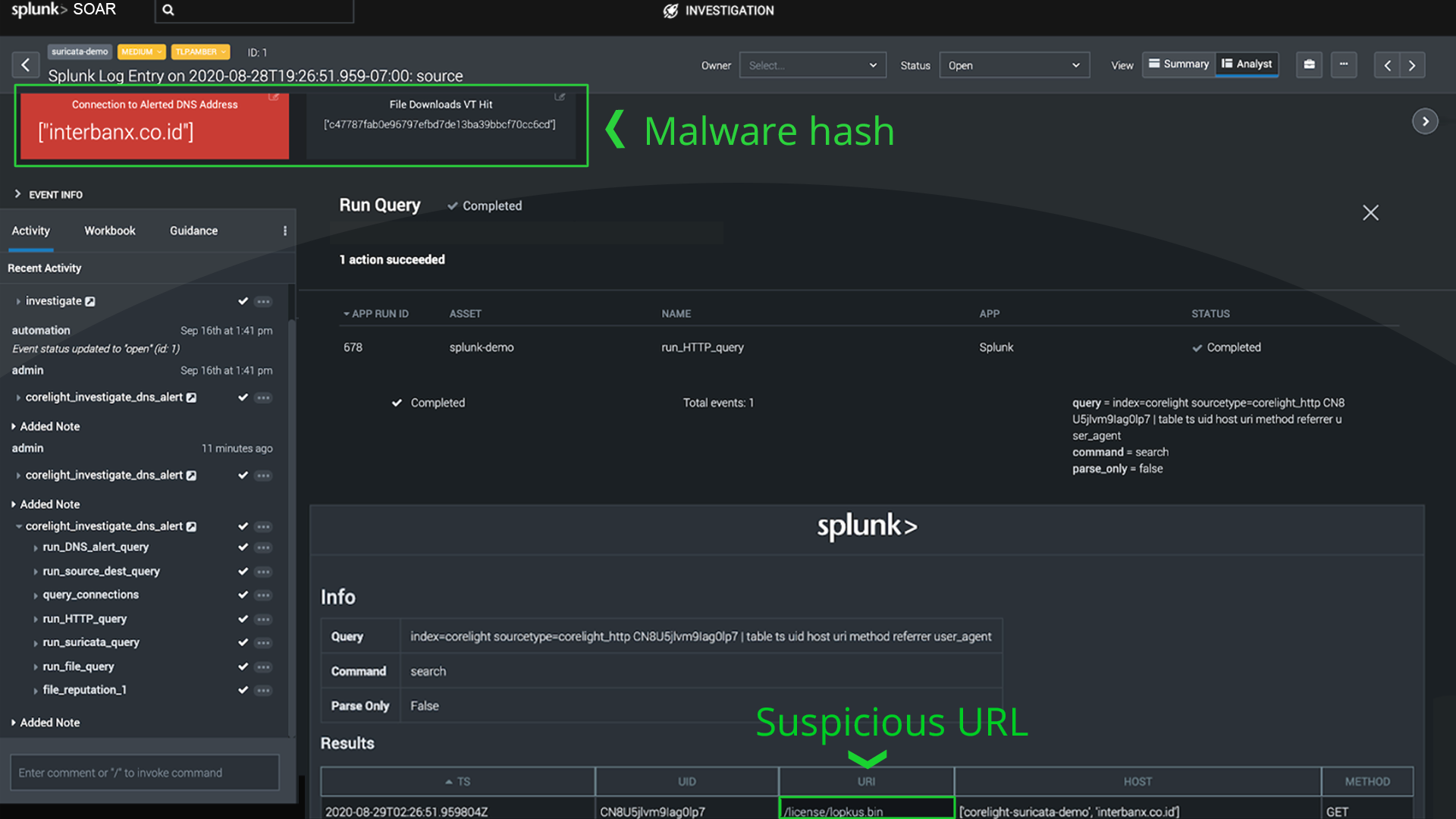
Easily validate true incidents
Successful attacks leave a trail of indicators - here, a known malware hash, a suspicious URL...
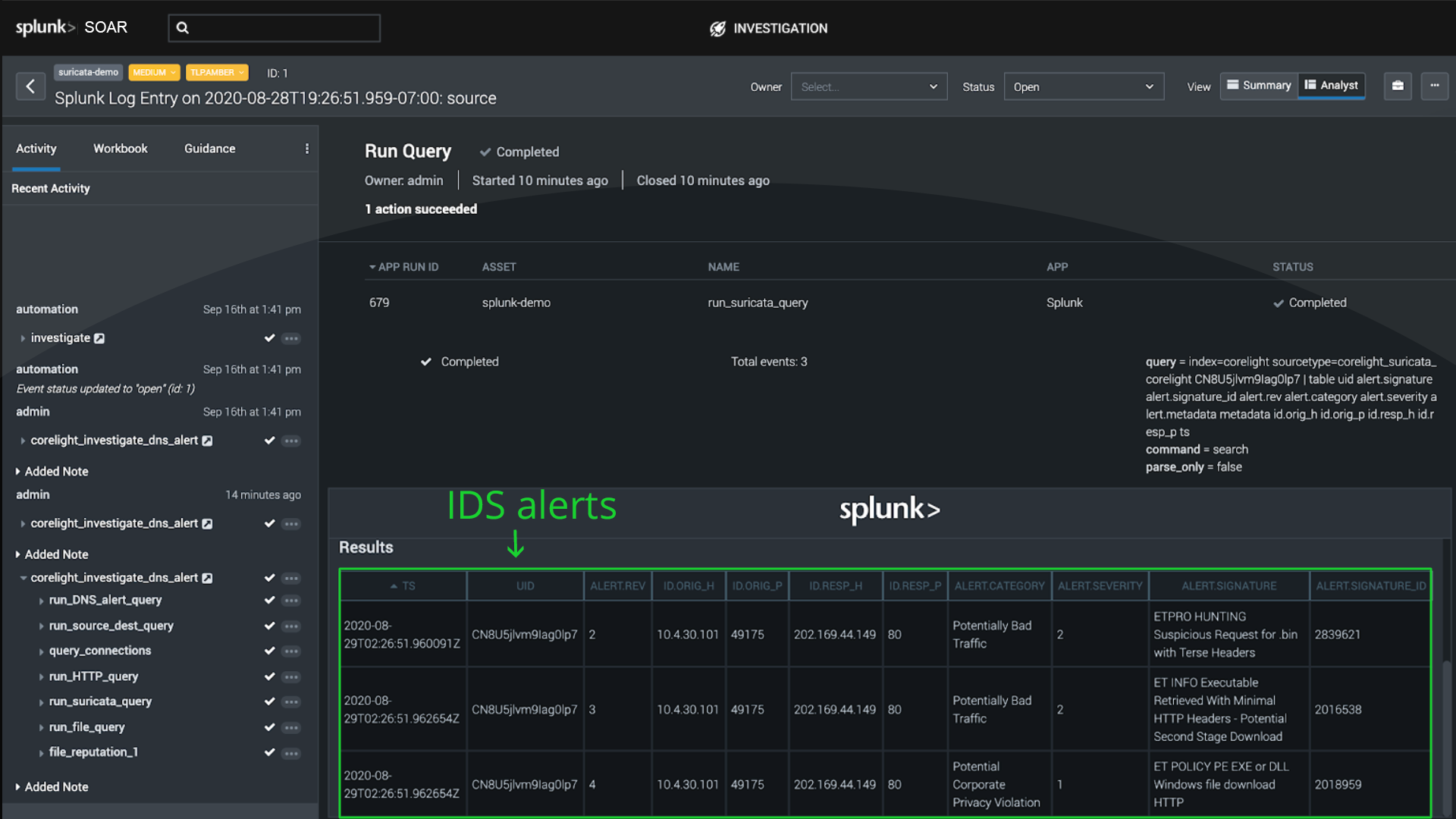
...and here IDS alerts. Corelight evidence, presented by SOAR, speeds decision making and reduces attacker dwell time.
Corelight and SOAR can transform your SOC
Schedule a call with an expert +1(510) 281-0760 or contact us