Investigator
Accelerate your workflow with automated daily triage

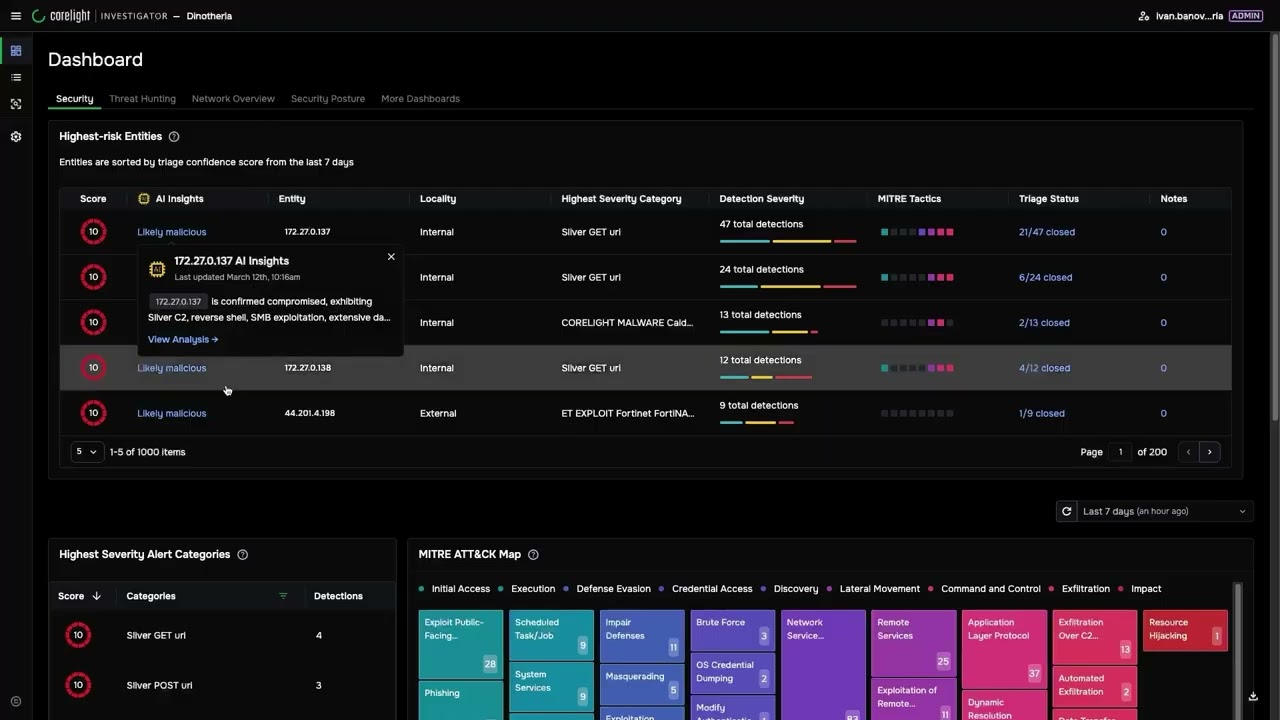
Agentic Triage with Investigator
Transform alerts into evidence-backed decisions.
Corelight Investigator simplifies complex network investigations with structured, expert-authored playbooks that automatically perform triage before analysts begin their work.
Instead of chasing fragmented alerts, analysts review entity-centric investigations grounded in expert-authored playbooks to ensure every investigation follows consistent, defensible triage logic.

Reduce triage time with autonomous triage
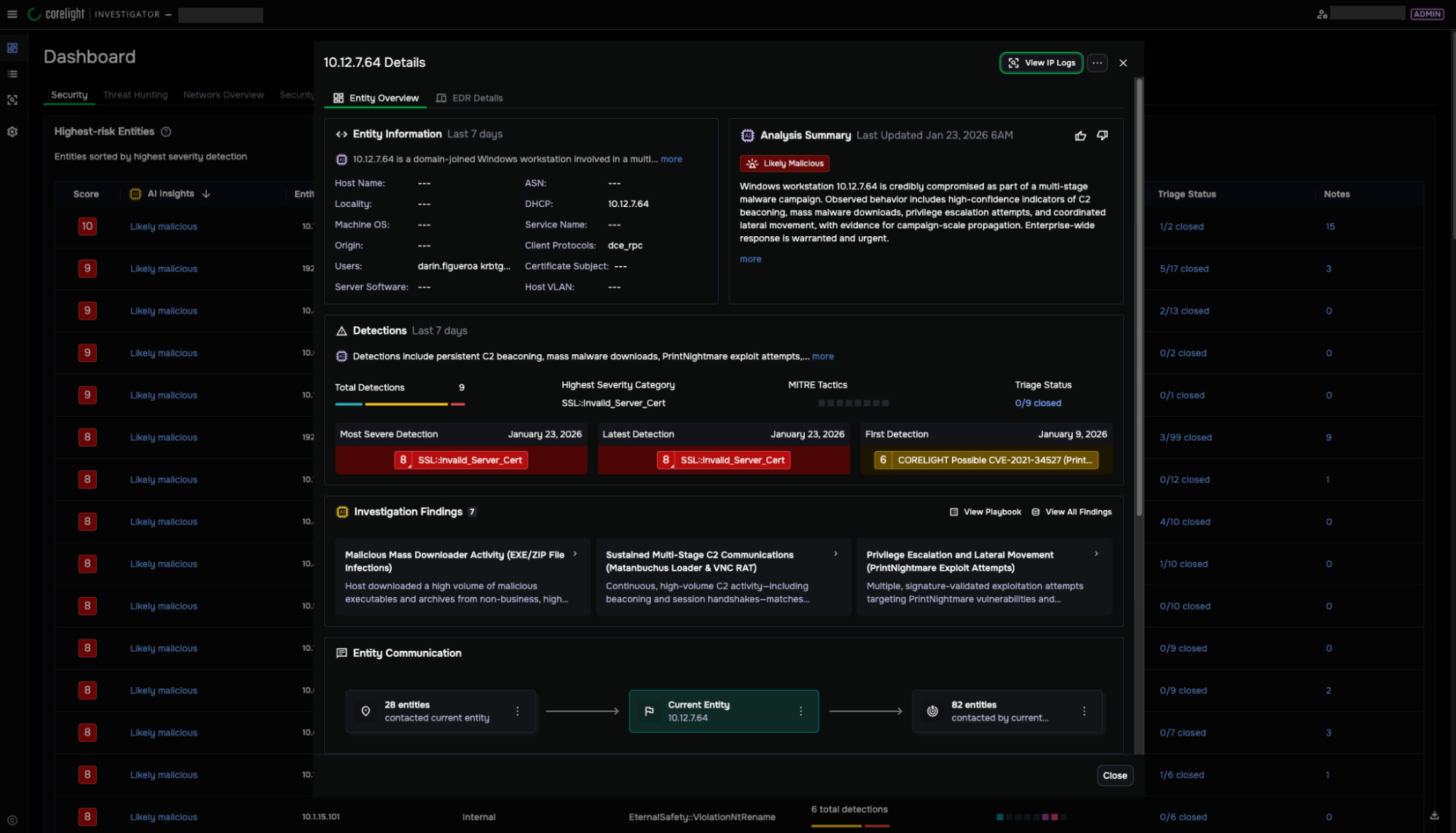
Corelight Investigator reduces investigation time by automating daily triage that consolidates and analyzes the top entities in your environment every 24 hours:
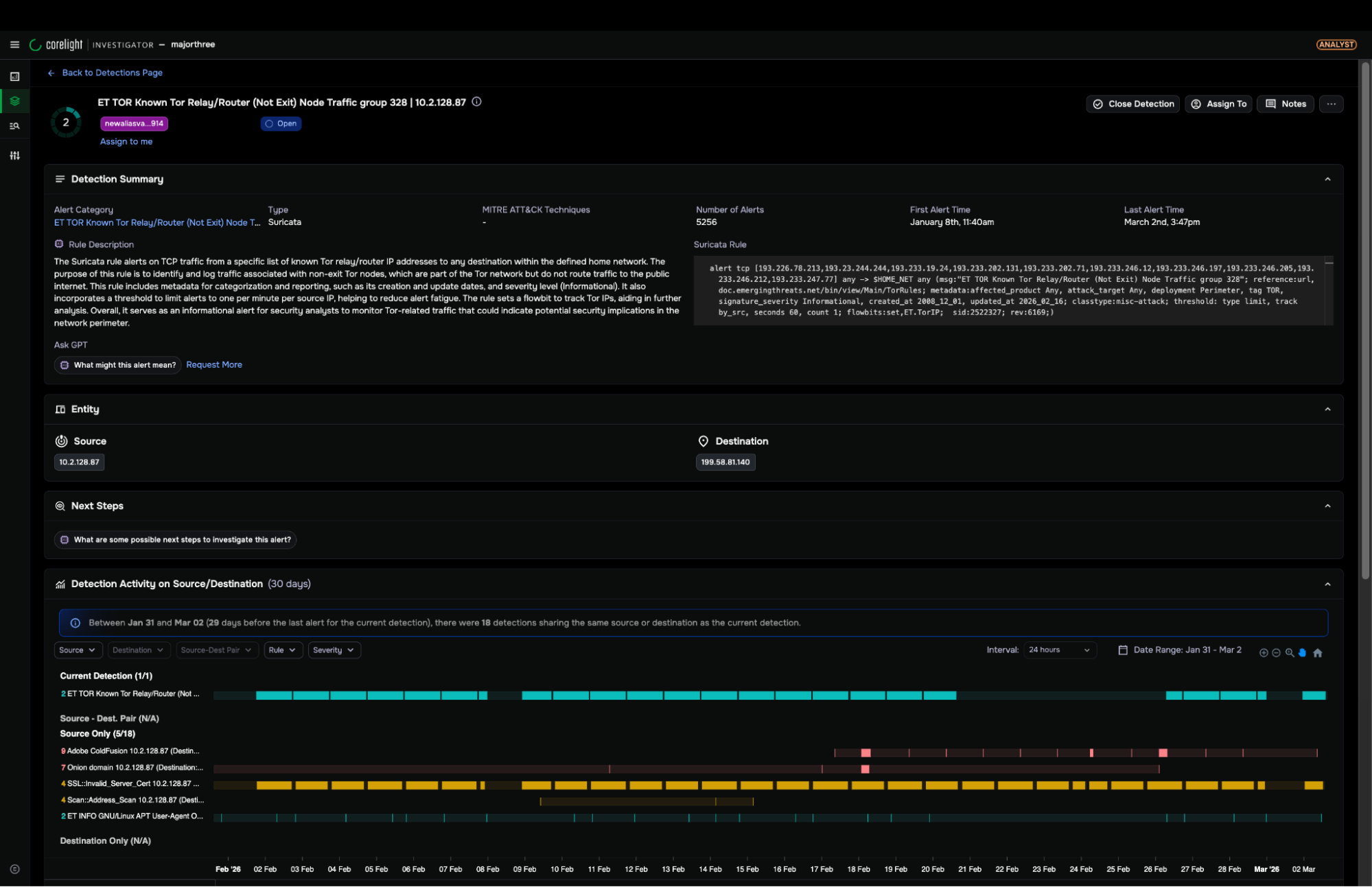
- Agentic Triage uses transparent, expert-written playbooks to follow consistent, defensible triage logic for every investigation
- Automatically investigates the last seven days of host activity to identify persistent patterns, lateral movement, and long-term TTPs
- Performs advanced detection correlation and analyzes dozens of raw log queries to unify disparate data points into a single narrative
- Provides analysts with a "ready-to-use" narrative, reasoning, and recommended next steps, eliminating the need for manual data stitching
Expand detection, validation, and coverage
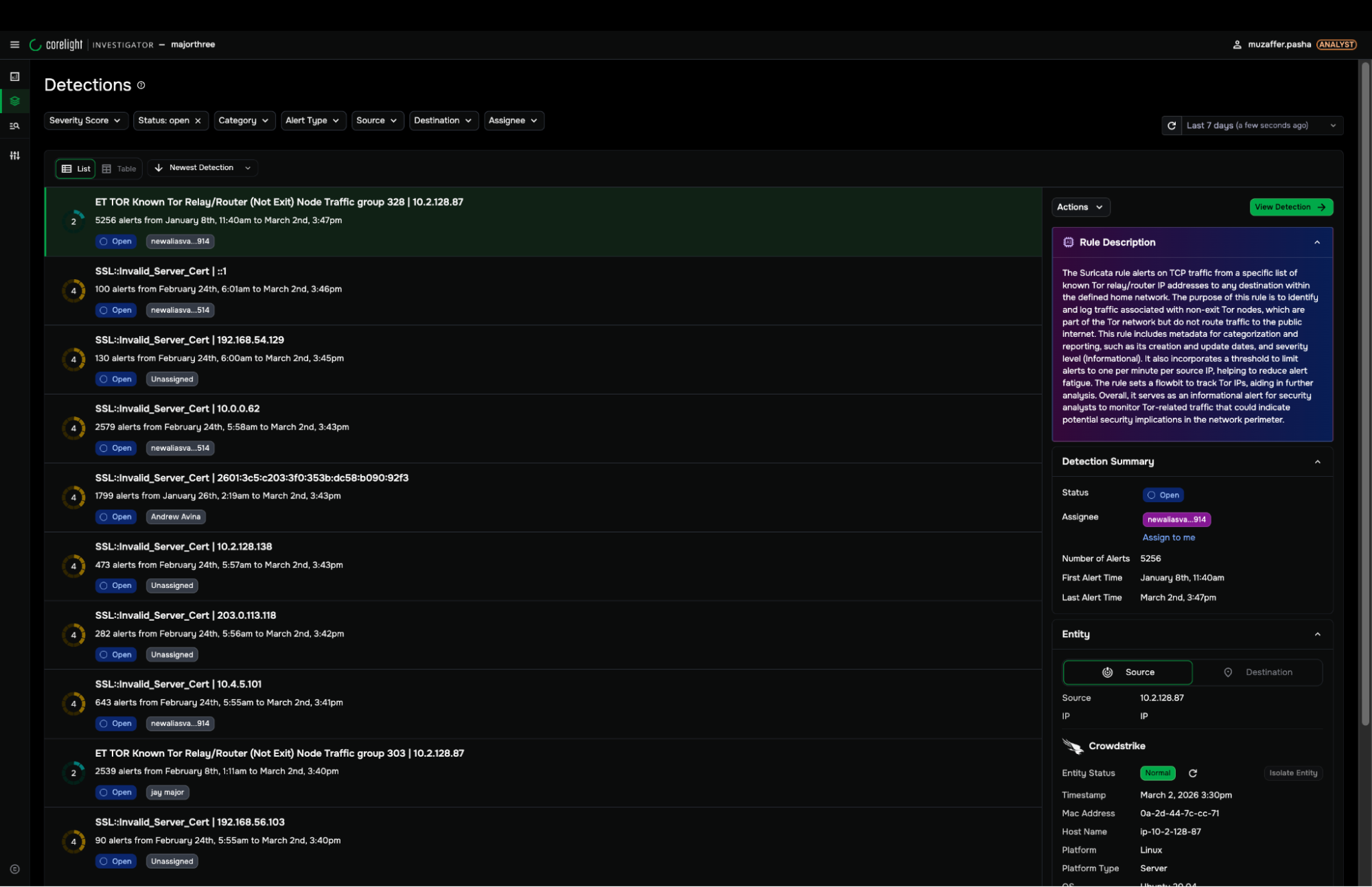
Investigator enhances detection impact by validating alerts through structured investigative workflows:
- Transparent AI/ML models
- Behavioral, signature, threat intel, and query-based detections
- MITRE ATT&CK® coverage across 100+ techniques
- Deep visibility into Defense Evasion, Credential Access, Discovery, and C2
Increase SOC efficiency with entity-centric investigation
Investigator empowers analysts to make informed decisions quickly by capturing all relevant data within a structured investigation framework. Automated playbooks, explainable AI summaries, and triage history reduce skill gaps and enable junior analysts to perform at senior levels:
- 3x more cases handled per analyst
- Toolset and dataset consolidation
- Single-screen, entity-based triage experience
- Out-of-the-box and customizable dashboards
- Easy access to raw data and GenAI summaries
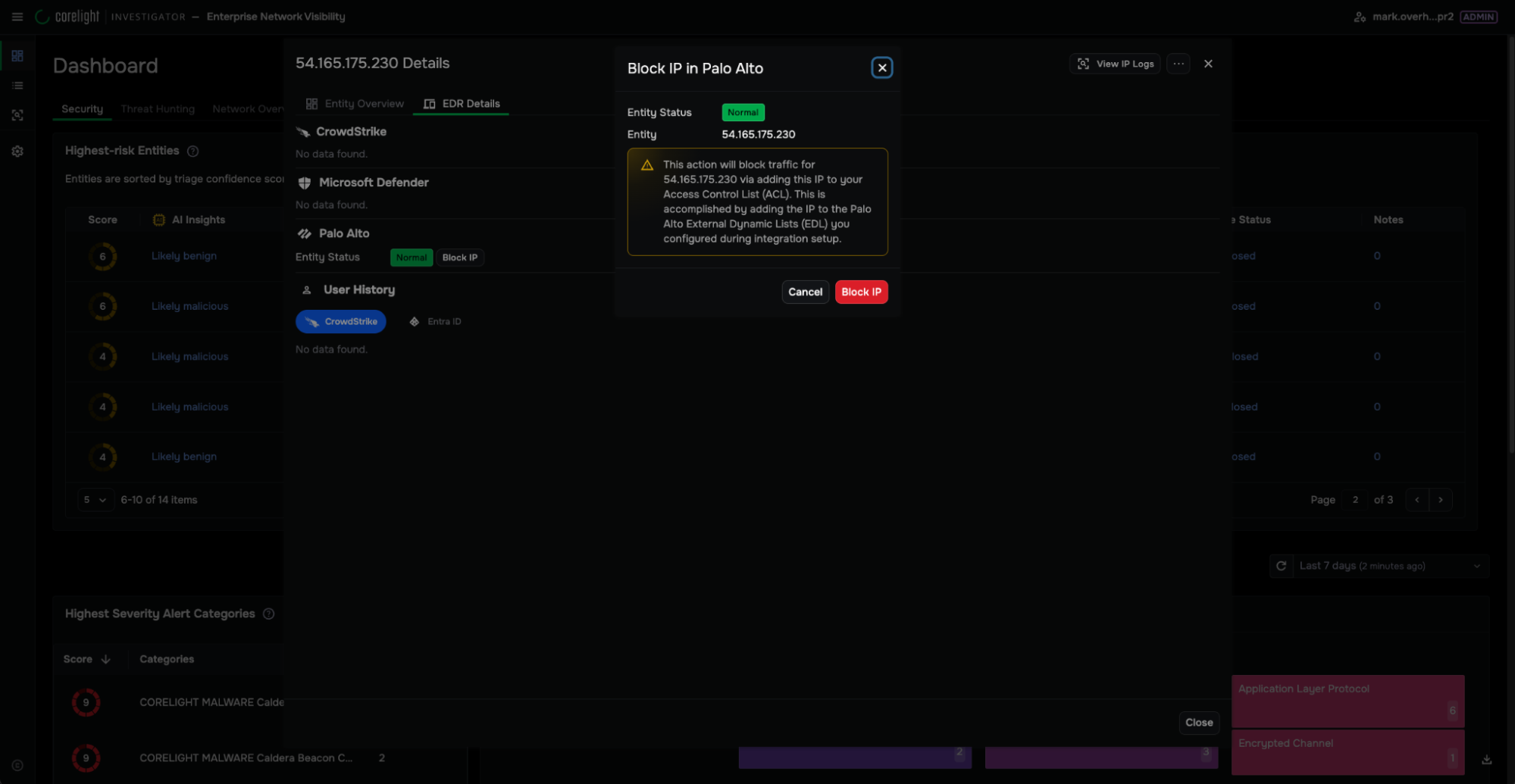
Enhanced response capabilities with built-in containment
Investigator allows analysts to move from verified investigation to response within the same interface. With a single click, analysts can isolate compromised hosts, enforce firewall policy changes, and trigger response actions directly from validated cases:
- Detection-to-response within one workflow
- One-click host isolation and containment
- Streamlined workflows that reduce response times
- Evidence-backed justification for every action taken
Triage with confidence
In this short demo, see how Agentic Triage helps SOC analysts filter through alerts and respond quickly to active threats.
- Transparent, expert-written playbooks for every investigation
- Host activity for the last seven days
- Ready-to-use narrative, reasoning, and recommended next steps
Breaches are inevitable—confident response is not
Our NDR Buyer's Guide provides the clarity to select the right platform and master crisis decision-making.
