Corelight at SC25: A laboratory for securing the fastest conference network
Defending the SCinet network is critical work. See how we handled orders of magnitude more traffic using Corelight’s Open NDR Platform.

Last month, Corelight had the distinct privilege of joining Cisco, NetWitness, Palo Alto Networks, Arista, and our internet service provider, MyRepublic, to provide availability and network security overwatch to the Black Hat Asia network in Singapore. This marked our first appearance in the Black Hat Network Operations Center (NOC). During the conference, four Corelighters covered traditional Security Operation Center (SOC) functions every morning from when the conference doors opened to when they closed for the day.
In this initial blog post, I'll cover the coordination it took to get to the event with our gear successfully onsite before arrival, the preparation required by so many individuals (to whom we owe our sincerest gratitude), and the key takeaways we'll be carrying with us into future Black Hat conferences. A forthcoming post will cover our NOC security-related findings from the Black Hat Asia event.
Three times a year, the Black Hat conference network has the potential to become one of the most austere, hostile networks seen on Earth. Given the sheer volume of malicious behavior on the wire, traditional signature-based detections can quickly overwhelm any analyst hoping to find evil from watching alerts for indicators of compromise (IoCs). A better practice is to adopt a threat-hunting mindset and search for anomalies, and this is where the visibility provided by Zeek and Suricata (which Corelight delivers in its commercial platform) shines brightest. As an informed reader, that last statement about using a traditional IDS platform such as Suricata for threat hunting may seem out of place, but rest assured, our included Corelight Labs & 3CORESec rulesets and the Emerging Threats Pro Hunting rules from Proofpoint provided opportunities to dig deeper into data we may not have initially seen on first glance.
Participating in the Black Hat NOC was also an opportunity for us Corelighters to colloquially "put our money where our mouths are" since we are usually highlighting elements of our products, showcasing new feature additions, or assisting customers and prospects on how to optimize their security stacks through visibility gains and detection engineering. This time we were going to be the end customer. From delivery to installation to configuration, it was on our team to ensure the first order was correct since many of the esoteric network supplies we may need are unavailable at a local box store. If you've ever traveled to Singapore, you may think, "Sim Lim Square or Sim Lim Tower would probably have something available," and you might be onto something. Still, we wanted to avoid testing that theory.
"Give me x hours to chop down a tree, and I will spend the first (⅔)x sharpening the ax."
- possibly Abraham Lincoln modified with a mathematical notation to adjust for the wildly different timeframes the Internet provided while investigating quote attribution.
When selecting gear for the event, we decided sensor redundancy was the key to success. We brought two Corelight AP 5000 sensors capable of up to 100 Gbps speeds. Was this overkill for the throughput of traffic we expected to monitor at the conference? Absolutely! Keep in mind that we were experimenting for the upcoming Black Hat USA show and also that our Corelight AP 1000, AP 3000, and AP 5000 sensors are all 1U appliances that essentially vary in the monitored traffic they're able to inspect: 20 Gbps, 35 Gbps, and 100 Gbps, respectively. Given that there would be zero shipping consequence going with the higher model number, our logistics team had them available, and that we'd be able to perform a parity test for the larger conference, we gladly opted for the AP 5000s.
In addition, we added our approved DELL ME storage array for Corelight Smart PCAP storage to the same pallet, along with twenty-six small form-factor pluggable (SFP) modules of varying media and transceiver types and cabling for each configuration. While onsite, we joked about potentially being over-prepared given the number of modules, fiber cables, MTP/MPO breakout cables, and direct attach copper cables we included in the order; however, it turned out to be a good thing since a couple of partners needed to borrow gear. The team also sourced an Intel NUC 12 Enthusiast transited in carry-on luggage to provide onsite access to Corelight Fleet Manager, LogScale as our local log repository (learn more about our strategic relationship with CrowdStrike), and IRIS, an open-source, collaborative ticket management, to catalog and action any exciting findings made by our Corelight team.
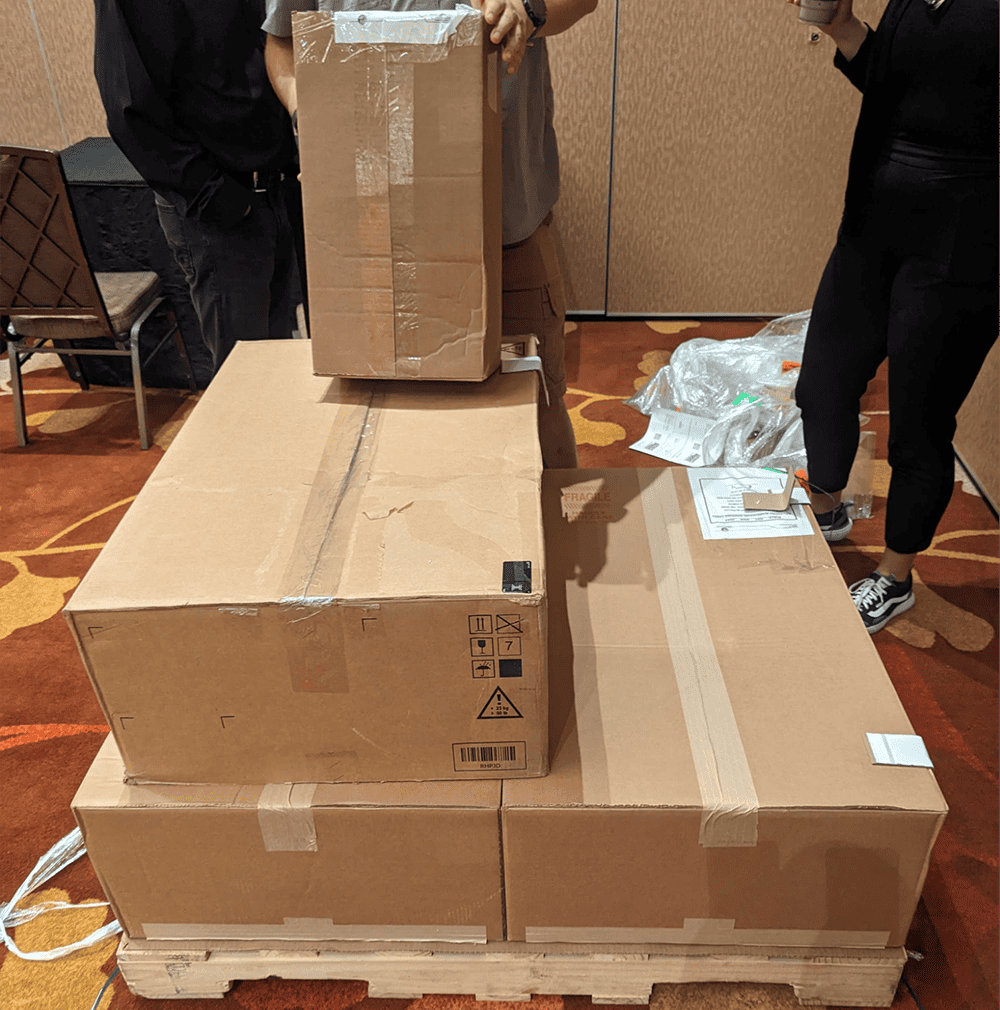
Thanks to our excellent logistics team and documentation writers, we were able to unbox, position, connect, and configure the equipment to start passively collecting data in under one hour after arriving at the NOC. Yes, we've all configured a Corelight Sensor in some capacity as part of our jobs, and we are deeply familiar with the software side of the Corelight platform. Still, before this event, I had personally connected and configured one Corelight sensor used in my home lab. The same was true for my other three team members as well.
Once our stack was fully operational, we began tuning the active sensor policy to scope traffic inspection further based on our standard Corelight packages, like Core Collection, Encrypted Traffic Collection, C2 Collection, and Entity Collection. We also sent all collected metadata to Investigator, our SaaS-based NDR solution. And in doing so, we experienced a few opportunities to give back to our Development and Engineering teams while leveraging these products to help enhance the customer experience in upcoming versions. It was a great feeling to be a part of such a positive feedback loop!
Another key focus of ours was to work on integrating with our NOC partners (Cisco, Arista, NetWitness, and Palo Alto), where we could help promote visibility and actionable outcomes and further strengthen our technology stacks by working together.
During the event, we:
We also set a stretch goal to integrate into Palo Alto's Cortex XSOAR platform to improve efficiency through automation and quicken the NOC's response to particular threats; however, we decided to roadmap that integration for the next conference because we rapidly found ourselves dealing with actual security events. Sound familiar? Yes, we're all susceptible to it.
We are excited to have participated in our very first Black Hat conference, with many more to come. Working in the Black Hat NOC with other highly effective teams was a great experience. We were able to network with experts from all over the world, better understand how different groups work together to protect attendees' information, and dig into some of the latest threats and attack trends.
Here are some of the fundamental lessons learned from our first conference:
Our team of Corelight threat hunters is grateful for the opportunity to participate in this event, and we're looking forward to future conferences, especially Black Hat USA!
Defending the SCinet network is critical work. See how we handled orders of magnitude more traffic using Corelight’s Open NDR Platform.
Corelight’s Open Network Detection and Response (NDR) solution has been chosen by the esteemed Black Hat Network Operations Center (NOC) to help...
Take a look at an incident we detected, investigated, triaged, and closed using Corelight at Black Hat Las Vegas 2023.