Turning the tables on the infiltrator
Learn how the kill web concept can be applied to cybersecurity, and how it addresses some of the concerns with the kill chain.
Editor’s Note (May 2025): This post has been updated to highlight how the Volt Typhoon and Salt Typhoon cyber-espionage campaigns exemplify that EDR evasion is real and why Network Detection and Response (NDR) is essential in modern defense strategies.
Over the last few years, the evolution of cybersecurity strategies has seen a significant shift toward a more layered, nuanced, and, in many cases, advanced approach. Among these advancements, Network Detection and Response (NDR) has emerged as a critical component that continues to become more widely recognized and accepted across the industry for its efficacy in bolstering cybersecurity defenses.
NDR’s recognition is underpinned by the SOC Visibility Triad, which advocates for a balanced integration of Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), and NDR.
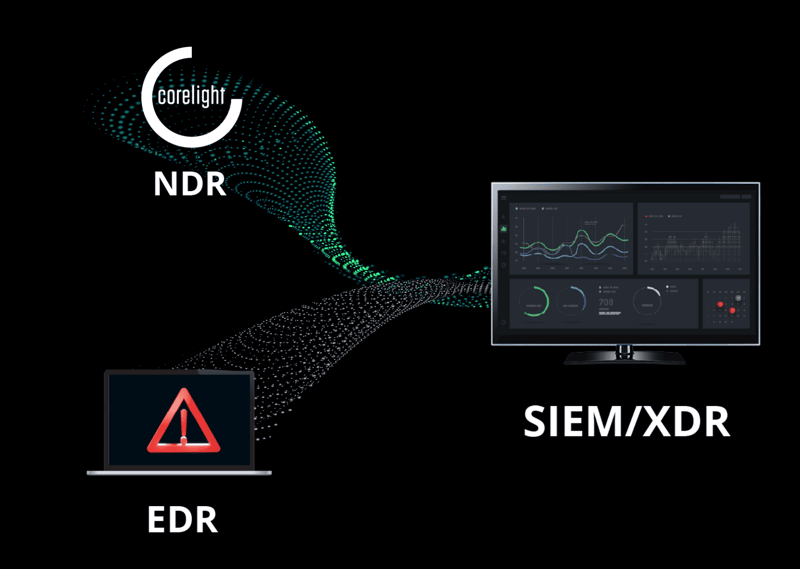
The SOC Visibility Triad underscores the importance of having diverse yet complementary security tools. NDR's role within this triad is pivotal, addressing gaps that EDR alone cannot fill and providing a more holistic view of network activity. The strategic integration of NDR with existing EDR solutions is not just an additive measure, but a transformative step in enhancing security operations.
As the digital landscape evolves and threats become increasingly sophisticated, the need for comprehensive security measures, such as NDR, is more important now than ever before. NDR's rise to prominence is a testament to its proven effectiveness in detecting and responding to threats that bypass traditional endpoint-focused defenses.
In this blog, I will explore the top 10 reasons why adding NDR to your defensive tool belt is crucial, even when EDR solutions are already in place. These reasons highlight the unique advantages of NDR, illustrating how it fills critical security gaps and improves operational efficiency.
Comprehensive visibility: EDR provides visibility into what's happening on your managed endpoints, but it doesn't offer insight into all network activity. NDR solutions fill this gap by providing visibility into network traffic, including encrypted traffic. This visibility allows for the detection of malicious activities that may not manifest in observable changes at the endpoint.
In the case of Volt Typhoon, these state-sponsored actors exploit vulnerabilities in internet-facing systems often beyond EDR's scope like routers and VPNs to gain initial access. NDR provides comprehensive visibility into such network activities, crucial for detecting these intrusions.
Adversaries can’t evade the network: EDR solutions are not infallible to zero-day attacks, supply chain attacks, advanced persistent threats, and nation-state actors. If an attacker can disable or bypass the EDR solution on an endpoint, that endpoint becomes blind to the attacker's actions. The network, however, cannot lie. Virtually all attacks must cross a network, and in doing so, attackers create a trail of network evidence. While adversaries can certainly obfuscate their network activity via encryption or by imitating legitimate traffic, they cannot avoid leaving behind evidence of these connections.
Volt Typhoon utilizes "living-off-the-land" techniques, leveraging legitimate tools like PowerShell and WMI to avoid endpoint detection. While these tools run on compromised hosts, their use for remote execution and lateral movement generates network activity, such as DCE/RPC and anomalous SMB or Kerberos traffic, that NDR can detect and flag for investigation.
Broader device coverage: EDR solutions can only monitor the endpoints on which they are deployed. Many EDRs are not designed to cover embedded devices or systems, IoT devices, Industrial Control Systems (ICS), Operational Technology (OT), and other unmanageable systems. An NDR solution provides an additional layer of security for every device on the network by monitoring traffic, potentially catching malicious activities on unmanaged endpoints.
Both Volt and Salt Typhoon target network appliances, devices typically not covered by EDR. NDR's ability to monitor all network traffic makes it indispensable for detecting threats on such devices.
Passive asset discovery and inventory: Without a clear understanding of what's on your network, it's challenging to detect anomalies or unauthorized access. NDR's ability to observe all network activity, not limited to just devices with EDR agents, endows security teams with additional identification capabilities for devices, applications, services, certificates, hosts, and more. This visibility helps identify devices unknown to their EDR, and empowers defenders to map and secure their environment more effectively based on real-time observation of the devices present rather than relying solely on presumed or expected data from an EDR, asset inventory, or Configuration Management Database (CMDB).
Threat actors like Volt and Salt Typhoon rely on internal reconnaissance to map networks and identify unmonitored devices and systems. NDR passively surfaces hidden assets, unexpected services, and lateral pathways, giving defenders the same visibility attackers are working to gain. As Rob Joyce, former NSA cybersecurity director and Corelight advisor, put it: “You have to know your network because your adversary absolutely will.”
Different detection capabilities: EDR primarily focuses on detecting and responding to threats on individual endpoints. It analyzes endpoint content, configurations, and behavior, and can identify potential threats and vulnerabilities. On the other hand, NDR monitors network traffic and analyzes network content and behavior, detecting potential threats that might not be fully visible at the endpoint level. This monitoring can detect lateral movement, command and control (C2) traffic, and other network visible indicators of compromise.
Volt Typhoon uses covert command-and-control channels like FRP (Fast Reverse Proxy) that often evade EDR because they appear benign, require no elevated privileges, and mimic normal outbound traffic. NDR can detect the tunnel behavior and unusual encryption patterns on the wire.
Risk-based alert prioritization: Most IT teams are unable to remediate every vulnerability, just as most SecOps teams are unable to respond to every alert. By merging or correlating network intrusion alerts from an NDR with vulnerability context from an EDR, SecOps teams can use a risk-based approach to prioritize response and tune out false positives.
While Volt and Salt Typhoon focus on exploiting unmanaged devices and lateral movement using valid credentials, EDR integrations with NDR support response by correlating suspicious network behavior with host context from EDR like MAC addresses, hostnames, or Active Directory (AD) affiliation and can even trigger host isolation to contain threats.
Enhanced investigation and forensics: NDR solutions can provide detailed network traffic logs, analysis, and packet captures, which are invaluable for post-incident investigations and digital forensics. While EDR provides endpoint-specific data, NDR adds a network-wide perspective, allowing for a more comprehensive investigation into how an attack occurred, what was impacted or exfiltrated, and the full scope of the breach. This is especially important for understanding complex or prolonged attack campaigns, verifying containment, and providing defensible disclosure.
Volt Typhoon exfiltrates AD databases using legitimate tools, which leaves minimal traces on the endpoint. They have also removed host artifacts such as event log entries and files to hide their activity. When attackers don’t leave host artifacts, packet data and connection logs become the only forensic record.
Integration and correlation: By integrating EDR and NDR, you can pre-correlate network data with endpoint vulnerabilities and other host data before it reaches the SIEM for a more rapid and comprehensive understanding of security incidents. Correlation using open standards like Community ID simplifies and accelerates the identification and analysis of complex multi-stage attacks, where the initial compromise might be visible on an endpoint, but subsequent actions, like data exfiltration, are more easily observed on the network.
Attacks like Volt Typhoon span multiple domains: network, identity, endpoint. By correlating NDR and EDR data can you piece together the full scope.
Support for zero trust architectures: As organizations move towards Zero Trust architectures, where trust is never assumed and must be continually verified, NDR solutions become even more critical. They provide ongoing monitoring and validation of network activities, confirming that only legitimate traffic is allowed and deviations from established norms are quickly identified and addressed. This complements EDR's role in securing endpoints under the same Zero Trust principles.
Salt Typhoon operates within trusted telco infrastructure. Their ability to live inside “legitimate” traffic paths underscores the need for continuous network validation. Zero Trust isn’t just about identity and endpoint posture. Network context is required to verify that behavior aligns with policy.
Compliance and regulatory requirements: Some industries and regulations may require or recommend both endpoint and network-level monitoring and response capabilities. Having both EDR and NDR solutions can help in meeting these regulatory requirements.
In the wake of campaigns like Salt Typhoon, CISA—along with agencies like the NSA and FBI—has issued detailed guidance emphasizing network visibility as a foundational defense. While not a traditional regulatory agency, CISA's advisories are shaping what regulators, auditors, and insurers increasingly expect, making NDR a practical requirement in critical infrastructure and other sectors.
Bonus reason: Attackers are deliberately evading EDR: One of the clearest lessons from the Volt and Salt Typhoon campaigns is that advanced adversaries are intentionally designing their operations to bypass endpoint defenses. They know you have EDR, and they operate around it.
In conclusion, a layered approach, blending the strengths of EDR's endpoint-focused insights with NDR's expansive network visibility, addresses the increasingly complex and sophisticated nature of cyber and OT security threats. NDR offers broad coverage across various devices, enhanced detection capabilities, and invaluable support for investigation and forensics.
Corelight’s Open NDR Platform combines dynamic network detections, AI, intrusion detection (IDS), network security monitoring (NSM), static file analysis, and packet capture (PCAP) in a single security tool that’s powered by proprietary and open-source technologies Zeek® and Suricata®, and YARA. You can read more about why customers trust our Open NDR Platform and support team to help defend their organizations on our Gartner Peer Insights page.
Learn how the kill web concept can be applied to cybersecurity, and how it addresses some of the concerns with the kill chain.
Learn how the kill web concept can be applied to cybersecurity, and how it addresses some of the concerns with the kill chain.
Avoid the 7 deadly sins of Network Detection and Response (NDR). Learn why firewall logs, black-box AI, and alert fatigue are killing SOC efficiency.