Corelight Splunk App update: New dashboard and data
We are pleased to launch our newest installment of the Corelight App for Splunk (Corelight App) and the Corelight Technical Add-on (TA).
Corelight sensors put your organization in the best position to watch over DNS traffic with a rich, powerful Network Traffic Analysis (NTA) data set. This article highlights the benefits of Corelight DNS logs, and demonstrates how Splunk Enterprise Security can reach a new level of functionality through integration with Corelight.
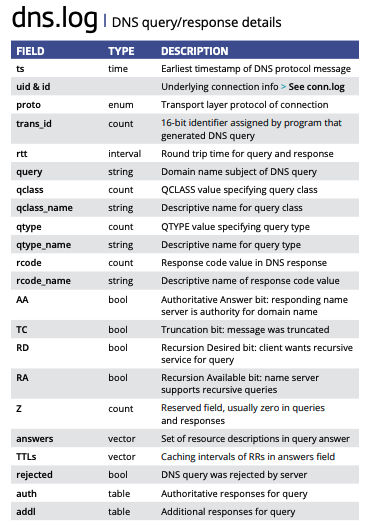
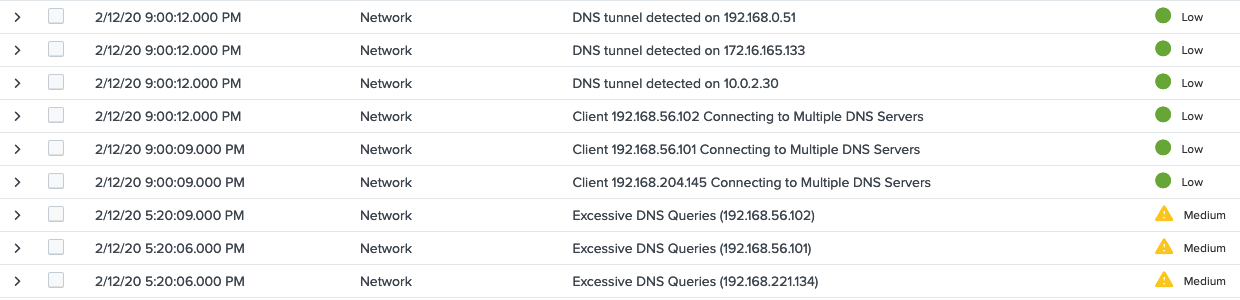
Corelight improves DNS monitoring in several ways, starting with extracting DNS metadata directly from packet data, to provide query and response in a single log. Corelight can dynamically detect DNS traffic, allowing you to monitor DNS traffic to external servers, see DNS traffic on non-standard ports, and more. Corelight DNS logs link directly to the connection log, enabling you to monitor DNS bandwidth usage, source ports, destination port, connection counts, and more.
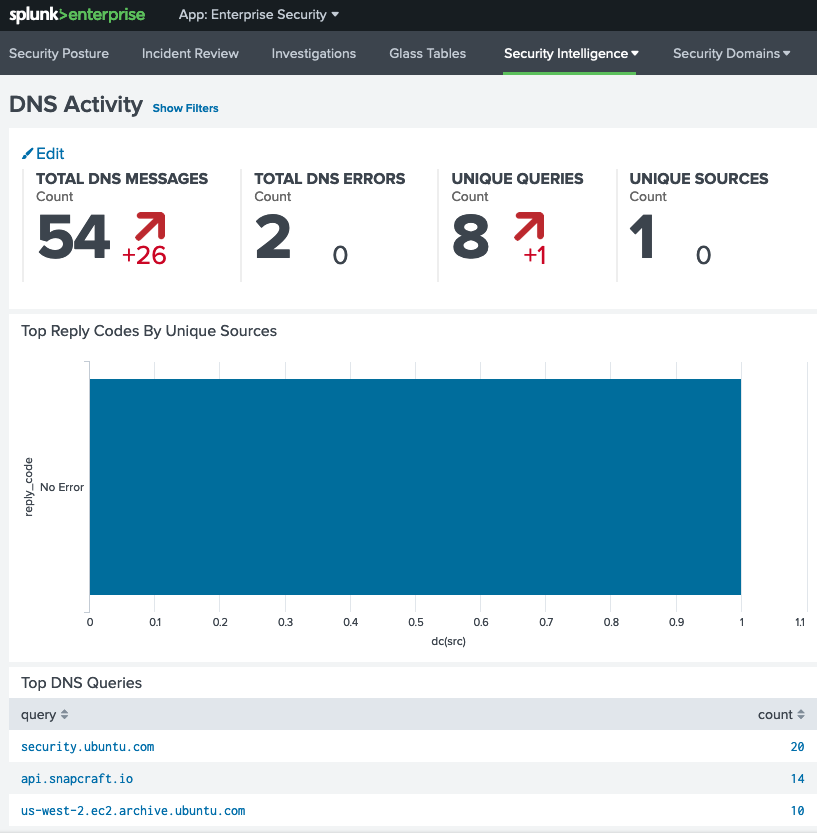
Corelight’s onboard Splunk integration means that data extraction and normalization happens out of the box. With Corelight App for Splunk and/or TA for Corelight, the data is also CIM compliant, allowing the data to populate the Network Resolution (DNS) data model for maximum efficiency at search time and in the Splunk Enterprise Security app.
Corelight App for Splunk: https://splunkbase.splunk.com/app/3884/
TA for Corelight : https://splunkbase.splunk.com/app/3885/
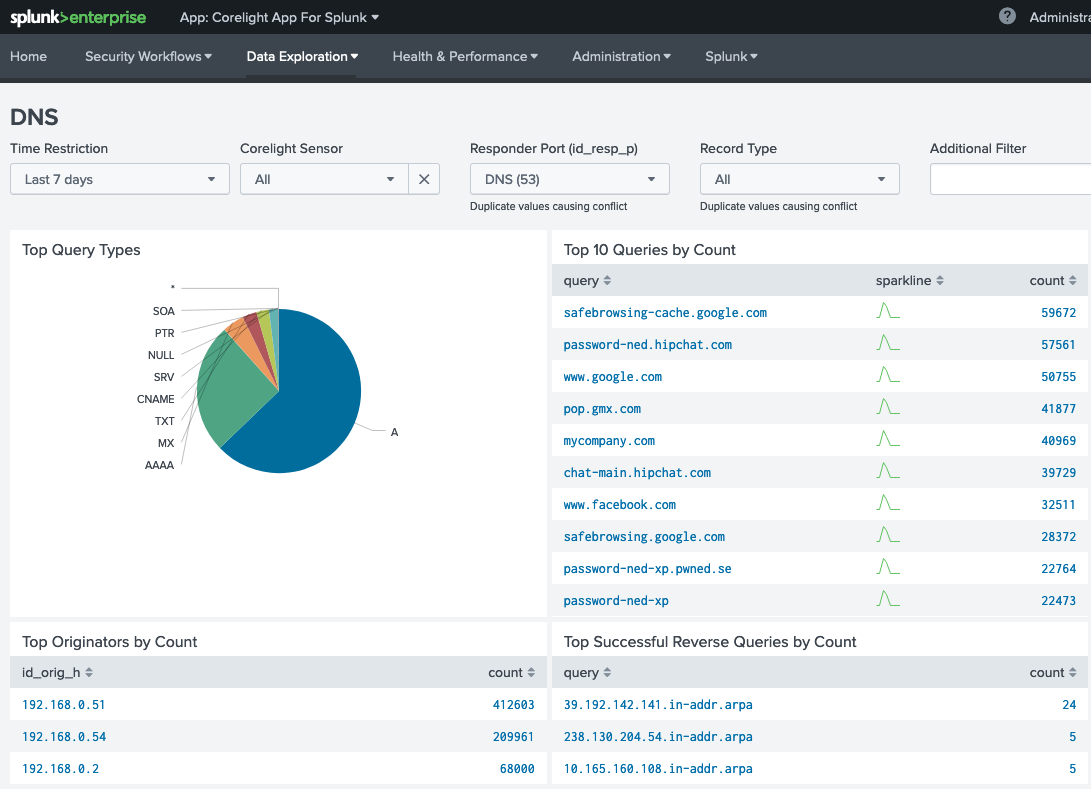
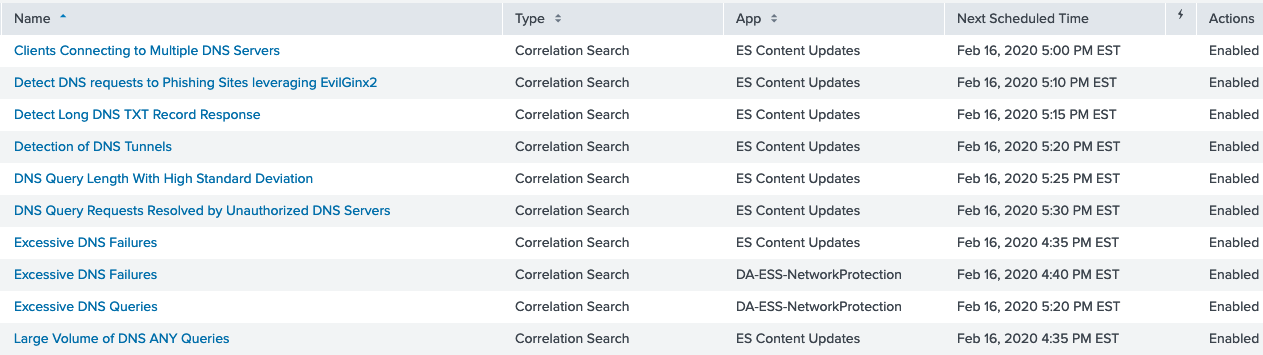
Many Splunk Enterprise Security deployments never realize the value of DNS workflows because they lack relevant, normalized data or can’t correlate data against other data sets. Corelight helps them overcome these challenges rapidly with built-in dashboards and correlation searches. It’s simple to correlate DNS data with network metrics like bandwidth, and from there, create advanced correlations that can identify and track complex attacks.
Don’t let DNS remain a blind spot. This solution is easy to deploy, data rich, and highly extensible. Corelight on Splunk gives you a sustainable advantage in looking at DNS traffic.
If you are a Corelight customer using Splunk Enterprise Security and want to realize the full benefits highlighted in this blog post, download our Splunk DNS Correlation Tech Brief for technical background, configuration specifics, and usage guidance.
We are pleased to launch our newest installment of the Corelight App for Splunk (Corelight App) and the Corelight Technical Add-on (TA).
I’m pleased to announce that Corelight sensors now support the Elastic Common Schema (ECS) via our Corelight ECS Mapping.
Are you looking to threat hunt but lack sufficient network and IDS data? Maximize your Splunk ES investment with Corelight.