Whether or not you made it to RSA 2023, here are two key themes we saw throughout this year’s conference.
Theme 1: #BetterTogether
As we looked across the show floor, it was clear that partnerships and integrations have more of a role in security than ever before, but determining which ones offer value can be challenging. Our team of experts demonstrated throughout RSA that fortifying enterprise-wide defense depends on extending network visibility across the enterprise, including both cloud and hybrid infrastructures. Together with our alliance partners, our Corelight experts showed attendees how leveraging network evidence within their existing tech stacks expands visibility, reveals attack scope, and reduces operational complexities and blindspots. Here's what CrowdStrike, Mandiant, Microsoft, and other Corelight partners had to say at RSA.
Expand visibility
Every adversary must cross the network. By this logic, network evidence should be a key component of any solid security program. We had the distinct honor of hearing this firsthand from our partners at CrowdStrike during RSA.
CrowdStrike’s Adam Hogan and Dixon Styres joined us in our booth to explain how Corelight NDR and CrowdStrike EDR enable a proactive defense, and why the Corelight-CrowdStrike partnership is one-of-a-kind, stemming far beyond technical integrations. During their presentations, Adam and Dixon illustrated how security teams are optimizing attack detection and disrupting adversaries by directly leveraging unified, long-term network and endpoint telemetry from Corelight and CrowdStrike within CrowdStrike LogScale.

Additionally, Dixon shared his unique experience using Corelight’s network telemetry, as he and his team use it regularly as part of CrowdStrike’s Incident Response Services. “Corelight helps us correlate high-fidelity network security telemetry which informs our incident responders and investigators of malicious threat activity hidden within the network,” said Dixon.

In fact, defenders were able to experience the power of Corelight and CrowdStrike during our Capture the Flag (CTF) incident response and threat-hunting simulation in the Dark Arts Village at RSA. CTF participants used correlated evidence from Corelight NDR and CrowdStrike EDR within CrowdStrike LogScale to test their threat investigation and DFIR skills.

Please let us know if your team would like to participate in a CTF event and experience the combined power of Corelight and CrowdStrike! Check out our webpage to learn how Corelight and CrowdStrike can help your team optimize attack visibility.
Reveal attack scope
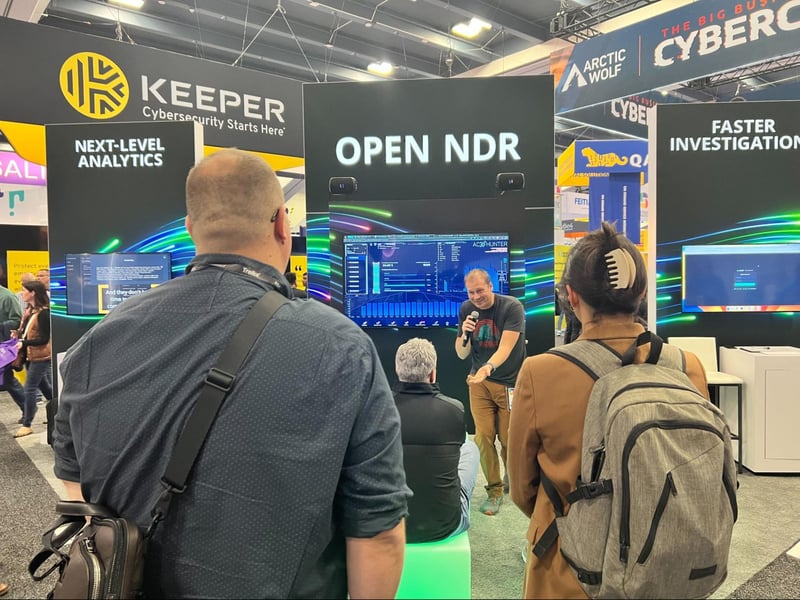
Keeping up with adversaries is difficult, but proper network monitoring helps defenders outmaneuver even the most dangerous of adversarial groups. Just take it from John Strand, CEO of Active Countermeasures—the creator of AC-Hunter. Luckily for us, John stopped by the Corelight booth to share how he used Corelight to identify a compromised instance of SolarWinds within a customer environment, long before the 2021 vulnerability was publicly disclosed. John also discussed how he regularly uses Corelight network evidence leveraged from Zeek® and Suricata IDS to perform threat hunts, and why he values open-source technologies in security.
Another guest speaker that we had the pleasure of hosting in our booth was Matt Bromiley, an instructor at the SANS Institute and Lead Solutions Engineer at LimaCharlie. Matt also talked about the importance of network monitoring and network evidence and most notably said this:
“Nearly every single attack out there is going to utilize the network, hands down. So if I'm omitting the network and I'm not using it, I'm missing the only required part. I can have an adversary come in via any operating system they want. I can have an adversary come in via any means they want remote access, exploit, drive by, spear phishing, whatever it is. But guess what? Once they're in, the network becomes the common ground. So we want to move our monitoring towards places like this and incorporate it with our other telemetry to make sure we're seeing everything we can.”

Want to see how defenders like John were able to detect SUNBURST activity and find SolarWinds backdoors? Watch this webcast and check out this blog for more.
And to learn why Matt has such confidence in the power of complete network visibility, Read this.
Reduce complexity, eliminate blindspots
Aligning your vendor strategy to key industry frameworks like MITRE ATT&CK helps reveal where your team may need additional coverage to accurately detect, identify, investigate, and remediate incidents. Getting the right coverage can help free up your team for proactive threat hunting and cyber defense. This topic came up in a range of partner presentations at the Corelight booth, including:

- Mandiant: Mandiant’s Alan White shared how Corelight and Mandiant are working together to accelerate detection and response across enterprise cloud and networks.
- Microsoft: Corelight’s Joe Gordon walked through our native Corelight-Microsoft integration for IoT and Sentinel, and how it reduces MITRE ATT&CK gaps with complete visibility across IT, IoT, and ICS networks.
- Cribl and CrowdStrike: Our own Geoff Kasten showcased how Corelight, Cribl, and CrowdStrike integrate to provide a powerful solution for advanced security observability and threat hunting.
- Splunk: Corelight’s Richard Chitamitre demonstrated how Splunk users can simplify threat detection and response by directly ingesting rich Corelight data into Splunk data models and dashboards.
- Palo Alto Networks: Our Corelight team co-presented with Palo Alto about a new Prisma Access feature that enables customers to replicate traffic from any application within their Prisma SASE environment to an external cloud-based service for forensic analysis, breach impact evaluation and threat signature profiling.
- Corelight’s John Gamble: John showed how to consolidate network security tools, reduce alert fatigue that drives staff turnover, and reduce the cost of post breach containment and remediation. Learn how our Open NDR Platform can help.
Theme 2: AI in security
The role of AI in security was another key topic during the show. Before RSA, we shared how we are leveraging AI and ML across our portfolio to enable SOCs to detect a broader range of sophisticated cyberattacks. We also announced a new industry-leading integration with OpenAI's GPT-4.
Here are a few key sound bytes from the announcement, which we talked about with RSA attendees in our booth and at the CTF:
"By leveraging GPT directly in our analyst experience, we are able to empower all users regardless of their sophistication to immediately recognize and understand complex attack patterns and potential remediations. As with many systems, the output is only as good as what you put in it, so there is plenty of opportunity for innovation. Our customers are telling us that our approach to GPT integration is solving a real problem, and this is only the beginning of what's possible." - Clint Sand, SVP of Product at Corelight
"Our newest ML analytics continue to expand the breadth of detection coverage at high accuracy, and our AI integration accelerates investigation and response — providing end to end assistance for security analysts. This is made possible because of the quality of evidence born from the Zeek project, which powers the most advanced network defenders globally." - Brian Dye, Corelight CEO
If you’d like to learn more about these new capabilities, contact us.
Missed RSA? Get a demo of Corelight.

Get a demo of Corelight, winner of Cyber Defense Magazine’s “Next Gen” Network Detection and Response (NDR) vendor award, to get the coolest shirt from the show.

