Threat detection
Illuminate and disrupt evasive attacks now reimagined with Agentic Triage. Detect advanced threats and automatically transform alerts into evidence-backed investigations with Open NDR built on forensic-grade network telemetry and explainable Agentic Triage.
Multi-layered detections
Corelight delivers a comprehensive suite of network security analytics that helps organizations identify more than 100 adversarial TTPs across the MITRE ATT&CK® spectrum. Corelight collects and analyzes contextual data and applies a multi-layered detection strategy that combines AI and machine learning, behavioral analytics, curated signatures, along with threat intelligence to deliver prioritized aggregated alerts based on risk.
Only Corelight provides explainability for machine learning detections and leverages the power of the global open-source community to deliver curated Zeek-based behavioral detections while providing detailed logs for hunting an attacker's trail with precision.
AI for Threat Detection — and AI for Investigation
Corelight’s AI/ML-powered detection engine uses supervised and unsupervised models to uncover advanced, evasive, and novel threats. Our models are customizable and never trained on customer data.
Beyond scoring alerts, Agentic Triage executes expert-authored investigative playbooks to validate detections with contextual network evidence.
Move from alert to decision—faster
EDR evasion and encrypted traffic coverage
Detect post-exploitation behavior and threats that evade endpoint controls—such as credential access, DNS tunneling, or anomalous SMB usage. See and detect across east-west traffic, unmanaged devices, and encrypted sessions, where EDR often has blind spots.
High-fidelity, low noise alerts
Targeted detections for high-value threat behaviors like lateral movement, C2 communication, encrypted traffic misuse, and exfiltration that are precise and context-aware - dramatically reducing false positives.
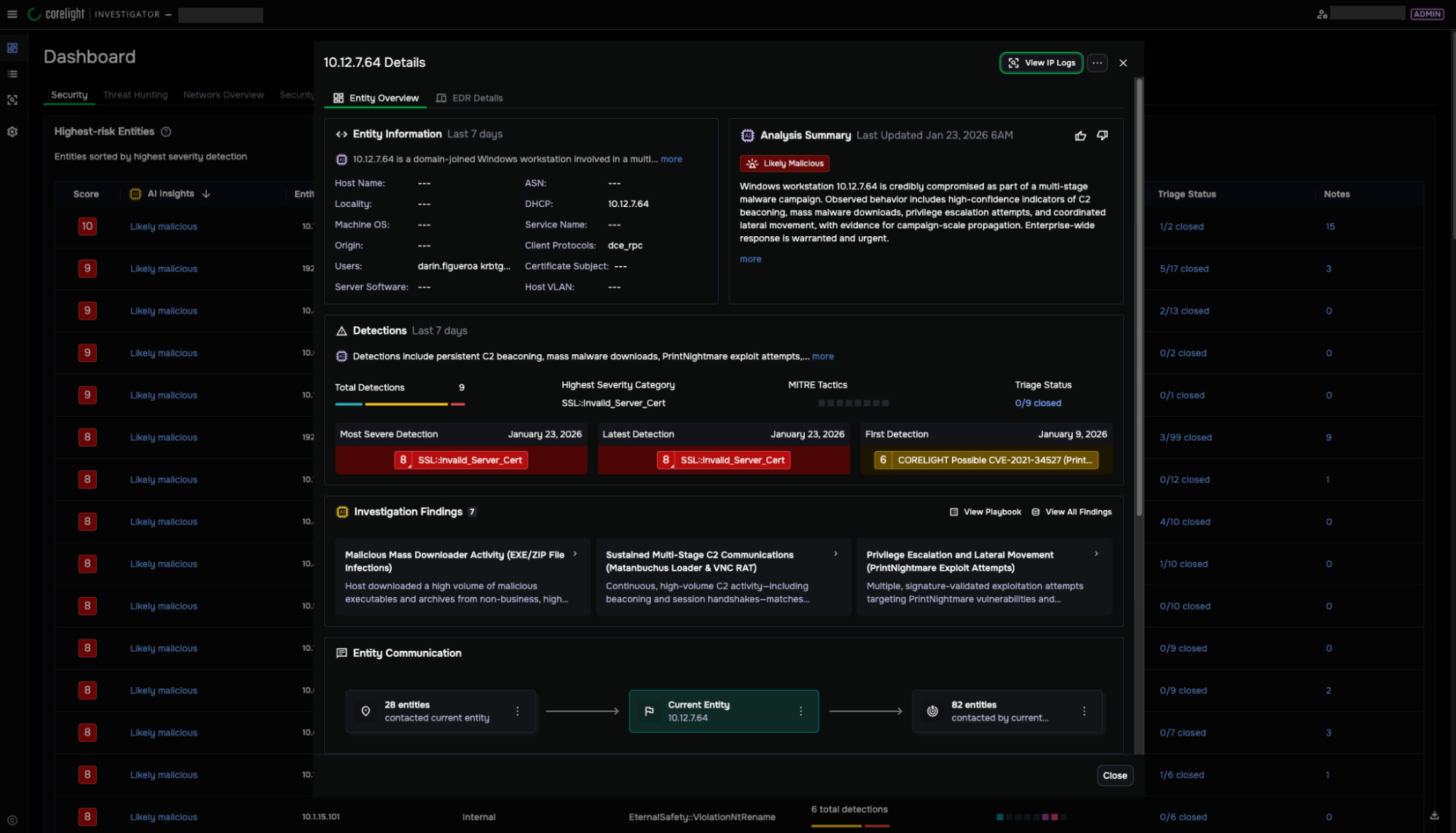
Automated triage with agentic AI
Agentic Triage consolidates related alerts into entity-centric investigations, automatically assembling evidence and producing defensible verdicts with visible reasoning.
Faster triage, quicker response with explainable AI
Corelight enriches detections with structured, AI-driven investigative workflows. Instead of manually correlating alerts, analysts receive:
- Pre-investigated entity cases
- Behavioral timelines
- Evidence-backed summaries
- Clear next-step guidance
- Transparent reasoning behind every conclusion
See the “why” behind every threat—so you can validate, contain, and respond with confidence.
The Corelight difference
- Backed by forensic-grade network telemetry for complete attacker visibility
- Targeted detections for high-value behaviors across the attack lifecycle
- Built on open frameworks to extend or customize detection logic
- Supported by curated, community-contributed behavioral detections
- Enhanced with Agentic Triage for consistent, explainable investigations

Top 5 reasons modern SOCs need multi-layered detections
Modern SOCs face sophisticated attackers, expanded attack surfaces, and pressure to do more with less.
Learn how combining multi-layered detection with Agentic Triage reduces investigation time and increases analyst efficiency.

Open NDR - integrated
analytics capabilities
Triage with Investigator—agentic workflow dashboard
Entity-centric investigations with explainable AI verdicts and evidence-backed summaries.
Network security monitoring with Zeek®
Complete visibility into every connection for analysis, investigation, and hunting.
IDS with Suricata®
Signature-based alerts enriched with Zeek® network evidence.
Static file analysis
Detect malware threats using YARA-based pattern detection.