- What is network traffic monitoring?
- How does network traffic monitoring work?
- How to monitor network traffic?
- A comparison of network monitoring tools
- Critical security use cases for network traffic monitoring
- Key challenges in enterprise network traffic monitoring (security focus)
- Advanced detection with network detection and response (NDR)
- Conclusion
- FAQ
Learn how network traffic monitoring captures flow and packet data to reveal threats, improve visibility, and accelerate incident response across distributed environments.
Visibility is paramount in today's distributed enterprise environments where data prevails as a primary target for malicious actors. For security professionals, a blind spot for monitoring of the network is a critical missing defense compromising organizational resilience, speed, and defense against threats. This is why network traffic monitoring—the practice of collecting, analyzing, and interpreting traffic flowing across a network—is not only a recommended best practice, but a foundational requirement for both security and operational excellence.
This article will define network traffic monitoring, provide suggestions to help monitor network traffic, and explore the advanced security capabilities that drive modern defense strategies.
What is network traffic monitoring?
Network traffic monitoring is the process of continuously observing the data flowing through a network infrastructure to gain insights into its performance, health, and security posture. It involves capturing, aggregating, and analyzing raw traffic data to identify patterns, anomalies, and potential issues.
There are two main goals for network traffic monitoring:
1. Performance and health
To ensure quality of service (QoS) by identifying bandwidth bottlenecks, high-latency links, or over-utilized servers, thus keeping business-critical applications running smoothly.
2. Security and forensics
To detect suspicious activity, unauthorized access attempts, and the internal lateral movement of threats that have bypassed perimeter defenses.
For comprehensive defense, security professionals require both.
| Feature | Performance focus | Security focus |
|---|---|---|
|
Goal |
Operational performance, capacity planning, and baseline health. |
Threat detection, incident response, and continuous risk assessment. |
|
Key Metrics |
Bandwidth utilization, latency, throughput, jitter, volume of data, top talkers, and application response time. |
Suspicious connections, failed login attempts, protocol anomalies, policy violations, known malware signatures, and command-and-control (C2) communication. |
|
Data Sources |
Flow data (NetFlow, IPFIX, sFlow), SNMP, and sometimes packet capture. |
Flow data, full packet capture (PCAP), IDS/IPS alerts, metadata generated from traffic analysis (e.g., DNS queries, HTTP headers). |
|
Tools |
Network performance monitoring (NPM) tools, and traditional packet sniffers. |
Network security monitoring (NSM), network detection and response (NDR), intrusion detection systems (IDS), security information and event management (SIEM). |
How does network traffic monitoring work?
The process of monitoring network traffic is a continuous cycle of data collection, processing, analysis, and alerting. It is the engine that drives network visibility.
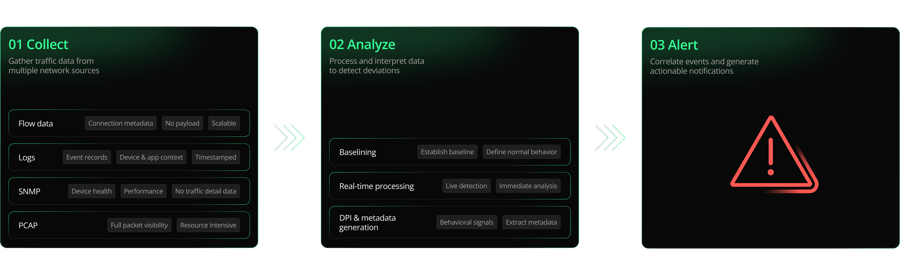
1. Data source collection
Effective network traffic monitoring relies on the following data sources:
- Flow data (NetFlow/IPFIX/sFlow): This is the most common method. Flow records summarize a conversation between two endpoints (Source IP, Destination IP, ports, protocol, timestamp, and byte/packet counts). They are highly scalable, consuming minimal storage, but lack the granular detail of the actual data payload.
- Log data: Logs provide event-driven records that offer context about network devices or application activities. They are timestamped records generated by operating systems, applications, and network devices (servers, firewalls, proxies) detailing events, errors, or status updates.
- Simple network management protocol (SNMP): This protocol queries devices (routers, switches, firewalls) for operational data, such as CPU load, interface status, and error counts. It provides health and performance metrics but is not suitable for deep traffic inspection.
- Packet capture (PCAP): Full packet capture involves recording every bit of data that traverses the network segment. This is the gold standard for monitoring network activity and forensic analysis, as it allows analysts to reconstruct full conversations and inspect malicious payloads. However, it is resource-intensive for storage and processing, making selective or metadata-generation strategies essential in large-scale enterprise network traffic monitoring.
2. Data aggregation and analysis
Once collected, the raw data must be processed:
- Baselining: The system establishes a baseline of "normal" traffic patterns. This baseline includes expected volumes, common protocols, and typical communications between hosts. This is crucial for detecting changes in network behavior.
- Real-time processing: Flow data is ingested and analyzed in near real-time network traffic monitoring to identify immediate deviations from the baseline, such as bandwidth utilization, latency, sudden, high-volume data transfers (exfiltration), or unexpected communication on non-standard ports.
- Deep Packet Inspection (DPI) & metadata generation: Modern security tools perform DPI on full packet streams to extract security-relevant metadata—like DNS requests, HTTP user-agents, and SSL/TLS certificate details—without retaining the entire, privacy-sensitive packet payload. This rich metadata (often called network evidence or logs) is the most important data source for NDR. It provides the context needed for behavioral AI to detect anomalies at scale.
3. Correlation and alerting
The monitoring system correlates traffic events with other data sources (logs, endpoint telemetry). When a threshold is crossed or an anomaly is detected, the system generates an alert, which can range from a low-priority notification about high link utilization to a critical alert about potential malware C2 activity.
How to monitor network traffic
Implementing an effective network traffic monitoring solution requires a structured approach, integrating both performance and security considerations. This instructional guide covers the necessary steps to check network activity and establish a mature monitoring program.
Step 1: Define the scope and critical assets
Before deploying any tools, clearly define what needs to be monitored and why.
- Map the environment: Identify critical network segments (e.g., data center, cloud workloads, remote access gateways).
- Identify assets: Focus monitoring efforts on high-value targets, such as domain controllers, core databases, and sensitive intellectual property storage. These assets require the most granular visibility.
Step 2: Choose the right data sources and collection points
Decide on the collection strategy:
- Flow data for scalability: Configure core routers and switches to export flow data (NetFlow/IPFIX) to a central collector. This provides a high-level view of how to view network traffic across the entire network.
- TAPs and SPAN ports for security: Use Network TAPs (Test Access Points) or switch SPAN (Switched Port Analyzer) ports to mirror traffic to a dedicated security sensor. TAPs are generally preferred in high-speed, critical links for a reliable, non-intrusive copy of the traffic. These mirrored traffic streams are then aggregated by Network Packet Brokers (NPBs), which act as an intelligent layer to filter, deduplicate, and load-balance the data before distributing it efficiently to dedicated security sensors.
Step 3: Select and deploy monitoring tools
Choose tools that meet the scale and complexity of your enterprise network. A common setup involves:
- A centralized network performance monitoring (NPM) system for performance data.
- A network detection and response (NDR) platform for deep security analysis.
Step 4: Establish security and performance baselines
Once data is flowing, allow the system time to learn.
- Performance baseline: Determine typical daily and weekly traffic volume, top-talking applications, and common error rates.
- Security baseline: Identify all internal and external services that hosts routinely communicate with. Any new, unsanctioned communication should be treated as suspicious.
Step 5: Implement alerting and automation
Tune the alerts to focus on high-fidelity security events.
- Prioritize anomalies: Focus on traffic that deviates significantly from the baseline (e.g., a desktop communicating with an external IP address for the first time, a sudden spike in DNS exfiltration attempts).
- Integrate with SIEM/SOAR: Forward high-priority security alerts to a central SIEM (Security Information and Event Management) system for correlation with endpoint and log data. Use SOAR (Security Orchestration, Automation, and Response) to automatically quarantine compromised hosts or block malicious IP addresses detected via traffic analysis.
A comparison of network monitoring tools
The tools used for monitoring network traffic vary significantly based on their primary focus (performance vs. security) and their ability to process raw packets versus flow data. Security professionals typically prioritize tools that offer deep packet visibility and advanced analytics.
| Tool category | Description | Key features | Best for |
|---|---|---|---|
|
Network detection & response (NDR) |
Security-focused platforms that ingest raw packet data, generate rich security metadata, apply behavioral analytics (AI/ML), and integrate with SIEM/SOAR. |
Full-scale visibility, protocol analysis, threat hunting, anomaly detection, real-time threat detection. | Advanced security operations, threat hunting, and detecting post-compromise activity. |
|
Network performance monitoring (NPM) |
Traditional tools focused on collecting flow data (NetFlow) and SNMP data to measure bandwidth and overall health. |
Capacity planning, QoS monitoring, latency tracking, identifying bandwidth hogs. | IT operations, network engineers, and performance optimization. |
|
Packet analyzers/sniffers |
Simple, open-source or commercial tools that capture and analyze traffic from a single network interface (e.g., Wireshark). |
Deep, forensic-level inspection of packet contents, protocol decoding, troubleshooting specific network issues. | Deep dive troubleshooting, root-cause analysis, and low-volume forensic tasks. |
Tools for network traffic monitoring (security focus)
- Network detection and response (NDR) platforms: These are the most effective modern tools for security-focused network traffic monitoring. They transform raw traffic into actionable security intelligence.
- Zeek® (formerly Bro): An open-source network security monitoring framework that generates rich, human-readable metadata logs (e.g., all HTTP requests, DNS queries, SSL certificates) from live traffic. It is a foundational component for many NDR solutions. The structured, comprehensive nature of this Zeek-generated data is critical because it provides the discrete data points (protocol, file hash, connection status, etc.) that machine learning models rely on to accurately build behavioral baselines and identify sophisticated, low-and-slow anomalies. It is a foundational component for many NDR solutions.
- Intrusion Detection Systems (IDS): A security tool designed to monitor network or system activities for malicious activity or policy violations. IDS tools function by comparing observed activity against a database of known attack signatures (signature-based) or by identifying deviations from normal patterns (anomaly-based), generating an alert when a potential threat is detected.
- Wireshark/tcpdump: Essential for forensic packet analysis when investigating a high-fidelity alert.
Critical security use cases for network traffic monitoring
Continuous monitoring of network traffic is essential for multiple defense functions:Detecting command and control (C2): Identifying C2 patterns by analyzing specific metadata fields, such as DNS query logs for rapid flux of newly seen domains (Domain Generation Algorithms) and connection logs for low-and-slow data transfer size and frequency, indicating malware calling home.
Identifying data exfiltration: Detecting sudden, massive data transfers to external, cloud, or unsanctioned storage sites that significantly deviate from the established traffic baseline.
Lateral movement detection: Monitoring internal traffic for evidence of an attacker moving from one compromised host to another (e.g., unexpected internal port scans, remote desktop protocol (RDP) connections between previously non-communicating hosts).
Key challenges in enterprise network traffic monitoring (security focus)
Despite its importance, effective enterprise network traffic monitoring presents several hurdles for security professionals:
- Encryption overload: The vast majority of internet traffic is now encrypted (HTTPS, TLS 1.3). This prevents standard deep packet inspection, leading to visibility gaps.
- Data volume and storage: In large environments, the sheer volume of traffic data (petabytes daily) makes full, long-term packet capture prohibitively expensive and complex.
- Alert fatigue: Poorly tuned systems can generate millions of alerts, forcing analysts to manually sift through noise, often leading to legitimate threats being missed. This challenge makes reducing false positives critical.
- Distributed environments: Monitoring traffic across hybrid and multi-cloud environments, remote workforces, and legacy on-premises systems fragments visibility and requires disparate tools.
Advanced detection with network detection and response (NDR)
To overcome the challenges of encryption and volume, modern network detection and response (NDR) platforms have become essential tools for security professionals. NDR offers security-relevant visibility where traditional methods fail.
The core advantage of NDR is its focus on protocol and metadata analysis rather than just raw packet content, especially for encrypted traffic.
- Protocol analysis without decryption: NDR tools can analyze the outer metadata of encrypted sessions. They look at TLS/SSL certificate details, server name indication (SNI), jitter, flow size, and connection frequency. For example, a host rapidly connecting to a series of newly registered domains with self-signed certificates is highly suspicious, even if the content remains encrypted.
- Behavioral AI and machine learning: NDR uses AI or machine learning models to analyze massive amounts of flow and metadata. These models excel at recognizing subtle deviations from normal behavior—a crucial step in reducing false positives in network traffic alerts. ML can detect the unique "fingerprints" of C2 communication or exfiltration without relying on static signatures.
NDR allows security teams to monitor encrypted traffic without decrypting everything, providing the necessary security insights while maintaining privacy and performance.
The NDR detection pipeline: from raw data to actionable alerts
At its core, NDR is a closed-loop system built on transforming raw network traffic into high-fidelity security events. This process formally follows a four-stage pipeline:
Visibility
Gaining full, reliable access to network traffic, typically via TAPs, SPAN ports, and Network Packet Brokers (NPBs).
Data
The crucial step where raw traffic is processed to generate rich security metadata (e.g., Zeek logs). This metadata abstracts the full packet, making it highly scalable, privacy-respecting, and the primary fuel for analysis.
Detections & anomalies
Applying advanced analytics (Behavioral AI/ML) to the metadata to establish a behavioral baseline and identify subtle deviations, policy violations, or known threat signatures.
Alerts & response
Generating high-fidelity alerts and integrating with tools like SIEM/SOAR to automate responses, such as quarantining a host or blocking a malicious IP.
The evolution to network detection and response (NDR)
Network detection and response has evolved from network traffic analysis (NTA)— the process of monitoring and inspecting network traffic patterns to identify anomalies or suspicious behavior, serving both performance troubleshooting and preliminary threat detection—and NSM. NDR solutions utilize advanced machine learning (ML), behavioral analytics, and continuous active monitoring to identify known and unknown cyber threats. Unlike passive monitoring tools, NDR automates protective actions, such as terminating suspicious network connections to disrupt an attack, and integrates seamlessly with Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) systems for rapid incident response.
For security professionals, solely relying on traditional performance network traffic monitoring tools that lack security correlation and deep behavioral analytics can be inefficient. The industry trend favors unified platforms that natively fuse performance context (NTM data) with deep security analysis (NSM data). This unification eliminates the blind spots and the operational burden associated with correlating data across disparate tools—known as "swivel-chair" monitoring.
Conclusion
Effective network traffic monitoring is non-negotiable for the modern security professional. By shifting the focus from simple performance metrics to deep, security-relevant analysis of network flows and metadata, security teams can gain the visibility needed to detect threats that have bypassed perimeter defenses. Implementing advanced tools like NDR ensures that the network remains the most reliable sensor for enterprise security.
To learn more about Corelight’s Open NDR Platform, visit our website.
Is network traffic monitoring the same as network security monitoring?
No. Network traffic monitoring (NTM) is primarily focused on performance, health, and capacity planning. Network security monitoring (NSM) is a security-focused discipline that uses traffic data (often supplemented by logs and endpoint data) to detect, investigate, and respond to threats. NSM is a subset and security application of the broader NTM practice.
What are the benefits of network traffic monitoring?
The primary benefits are:
- Faster incident response: Provides the evidence (the "flight recorder") necessary for forensic investigation.
- Proactive threat detection: Identifies anomalous behavior that signature-based tools miss.
- Capacity planning: Allows IT teams to optimize network resources and defer unnecessary hardware upgrades.
- Reduced downtime: Quick identification of network bottlenecks and resource saturation.
Which metrics should I track when monitoring network traffic?
- For security, focus on these metrics: New external connections, communication on non-standard ports, unexpected protocols, and geographic anomalies.
- For performance, focus on these metrics: Interface utilization (in/out bytes), top talkers (highest volume hosts), application response time, and packet loss/error rates.
How can I monitor encrypted traffic without decrypting everything?
Modern security tools, particularly NDR platforms, use advanced techniques:
- Metadata analysis: Inspecting unencrypted elements of the session (e.g., DNS queries, SNI fields, certificate details) to infer intent.
- Flow and behavioral analysis: Utilizing machine learning to analyze the size, frequency, and timing of the encrypted connections to detect C2 channels or data exfiltration, which have distinct, observable traffic characteristics.
How much data should I retain for historical traffic analysis?
Data retention is a balance between compliance and cost.
- Flow/metadata: It's recommended to retain aggregated flow and security metadata (e.g., Zeek logs) for 6–12 months or longer for regulatory compliance and advanced threat hunting. This data is small and highly valuable.
- Full packet capture (PCAP): Due to storage costs, PCAP is typically retained for a shorter period, often only a few hours to a few days, and only on the highest-priority network segments. Analysts should retrieve and archive relevant PCAP files immediately upon an alert.
Can AI or machine learning improve network traffic monitoring accuracy?
Yes. AI and machine learning are fundamental to modern network traffic monitoring. They establishan accurate baseline of normal network behavior faster than human analysts and can automatically detect subtle, evolving anomalies—such as a shift in internal lateral movement tactics—that would be missed by static thresholds, thereby significantly improving detection accuracy and reducing analyst effort.
Book a demo
We’re proud to protect some of the most sensitive, mission-critical enterprises and government agencies in the world. Learn how Corelight’s Open NDR Platform can help your organization mitigate cybersecurity risk.